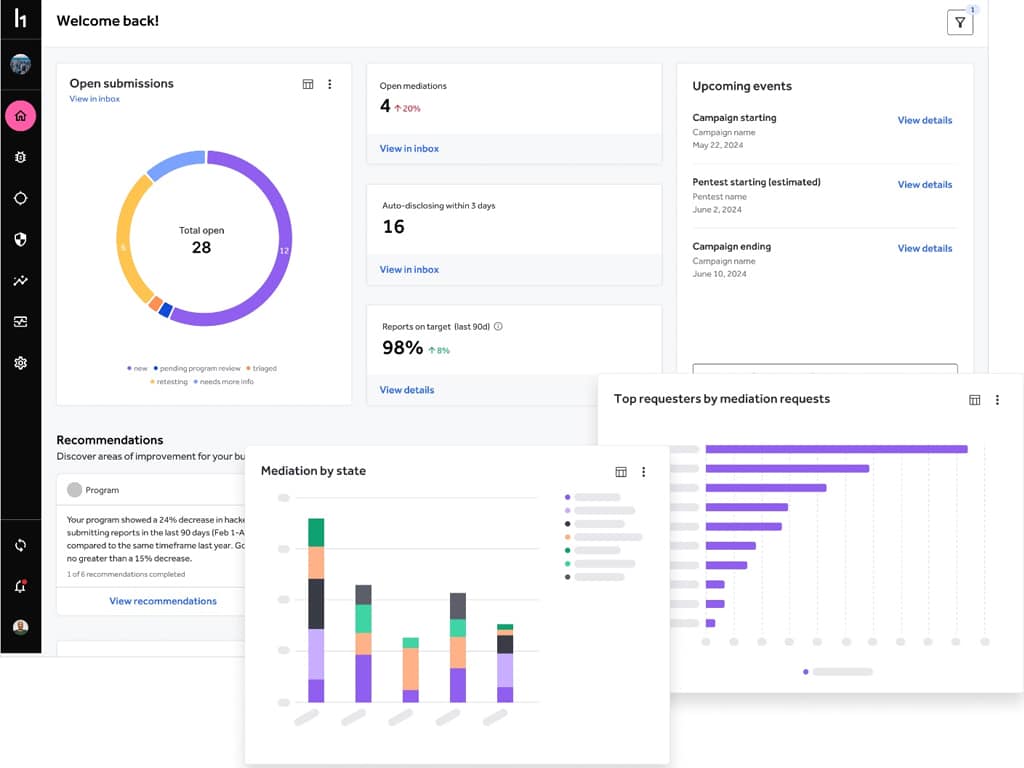
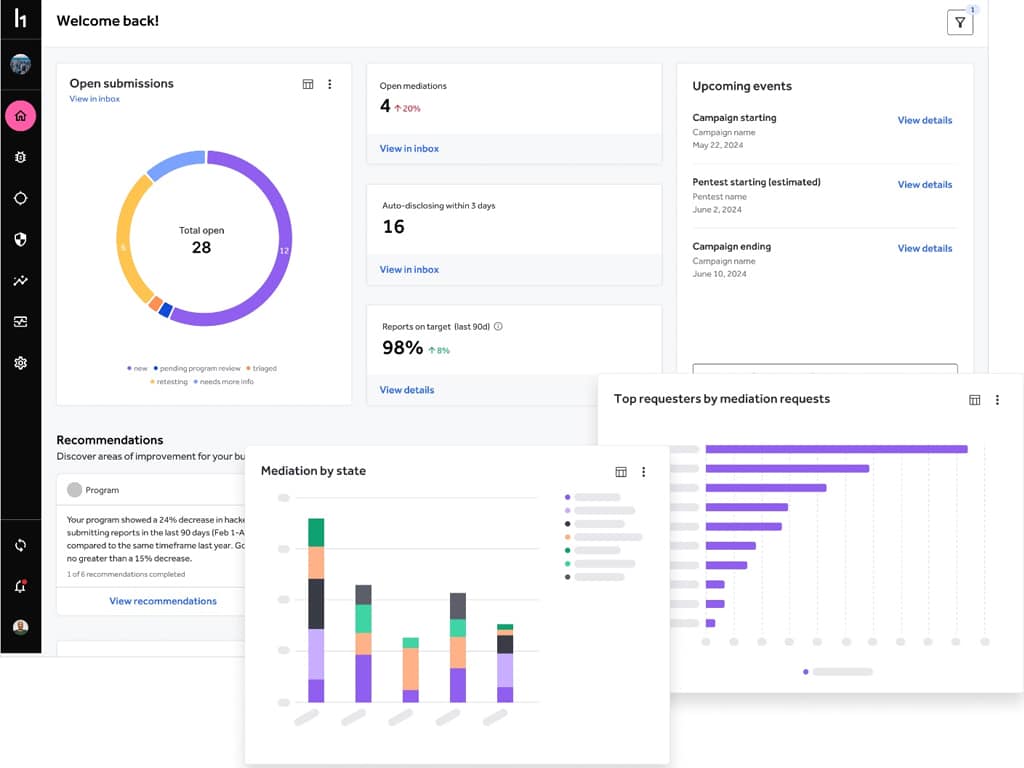
 I was thrilled to catch up with HackerOne during Black Hat USA 2024. The modern threat landscape presents increasingly complex cybersecurity challenges for modern organizations. Emerging technologies, like generative AI,…
I was thrilled to catch up with HackerOne during Black Hat USA 2024. The modern threat landscape presents increasingly complex cybersecurity challenges for modern organizations. Emerging technologies, like generative AI,…
The post Publishers Spotlight: HackerOne appeared first on Cyber Defense Magazine.
