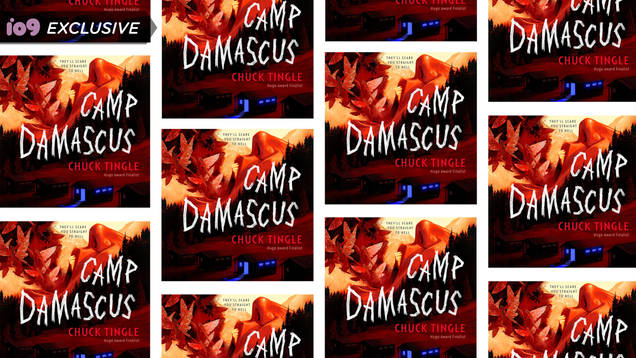
Chuck Tingle is known for his cheeky erotic comedies which he first started publishing in 2014. For his first full-length, traditionally published novel, Tingle has turned to a different set of inspirations. Horror movies, sleepaway summer camp stories, and queer survival are all a part of Camp Damascus. And now, io9…
Read more…
