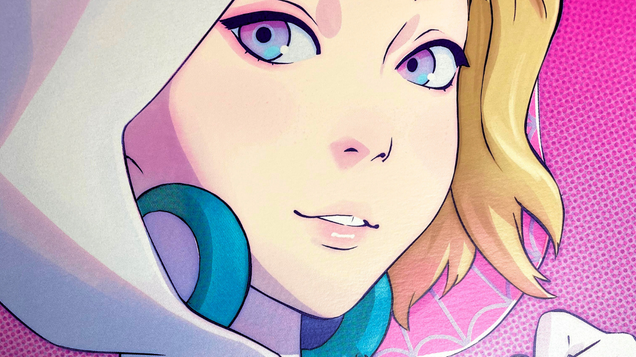
When Spider-Man: Across the Spider-Verse hits theaters tonight, one thing is very clear from the very first scene. This is not simply a Miles Morales movie. It’s a Gwen Stacy movie too. The film starts with Gwen, gives her more context, backstory, and a heck of a lot of very difficult to problems to deal with along…
Read more…
