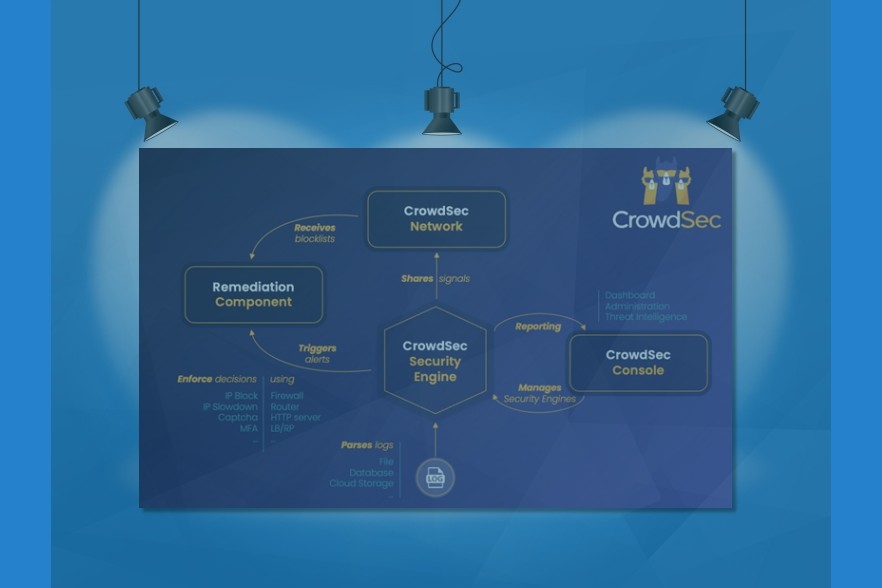
CrowdSec is a modern, collaborative cybersecurity company committed to proactively safeguarding digital assets. With a growing community of 65,000+ active installations contributing to a robust, constantly-updated global IP reputation database […]
The post Publisher’s Spotlight: CrowdSec: Real-time & Crowdsourced Protection appeared first on Cyber Defense Magazine.