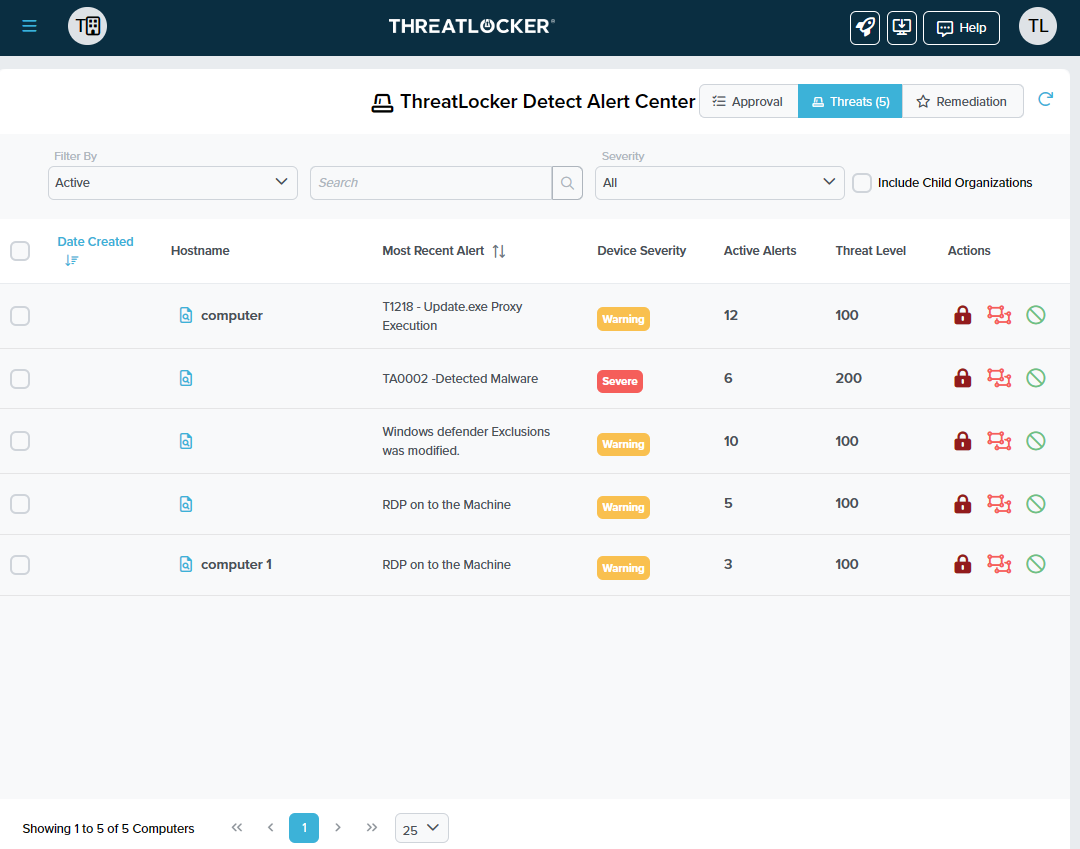
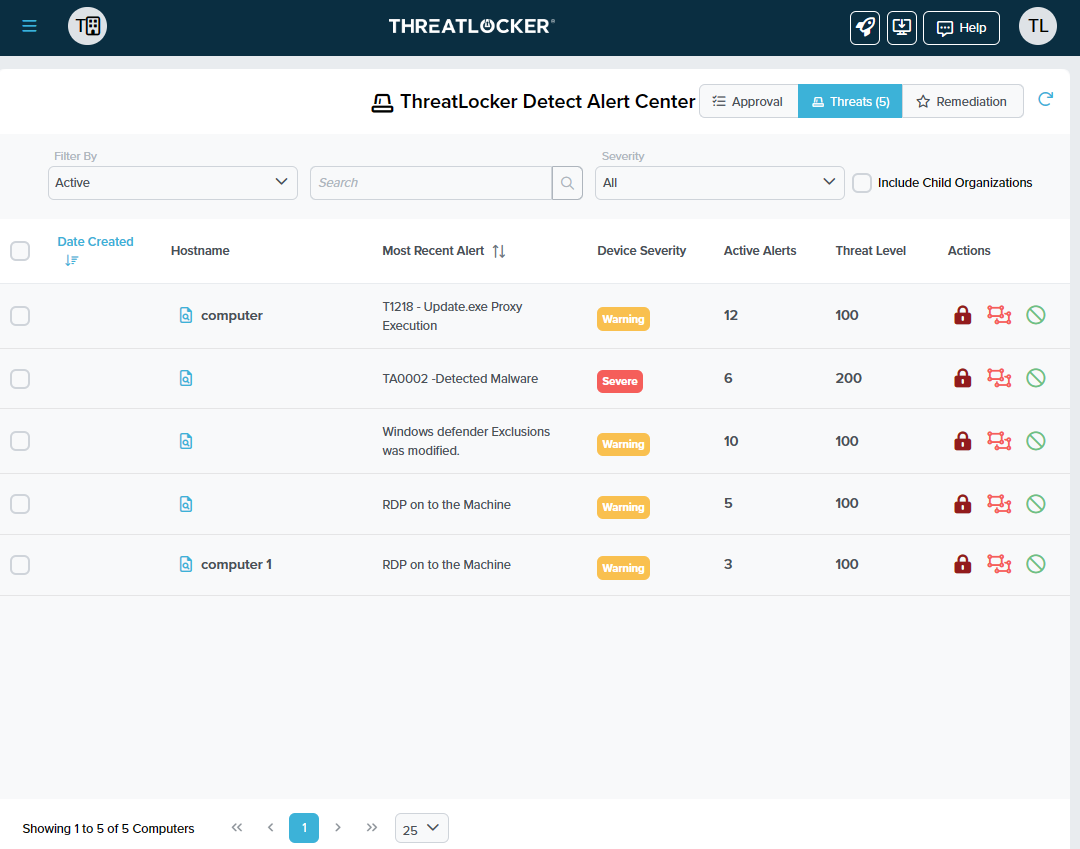
 In the rapidly evolving world of cybersecurity, incidents frequently arise when malicious code finds its way into trusted environments. These breaches can be triggered by seemingly harmless actions, such as…
In the rapidly evolving world of cybersecurity, incidents frequently arise when malicious code finds its way into trusted environments. These breaches can be triggered by seemingly harmless actions, such as…
The post Innovator Spotlight: ThreatLocker appeared first on Cyber Defense Magazine.