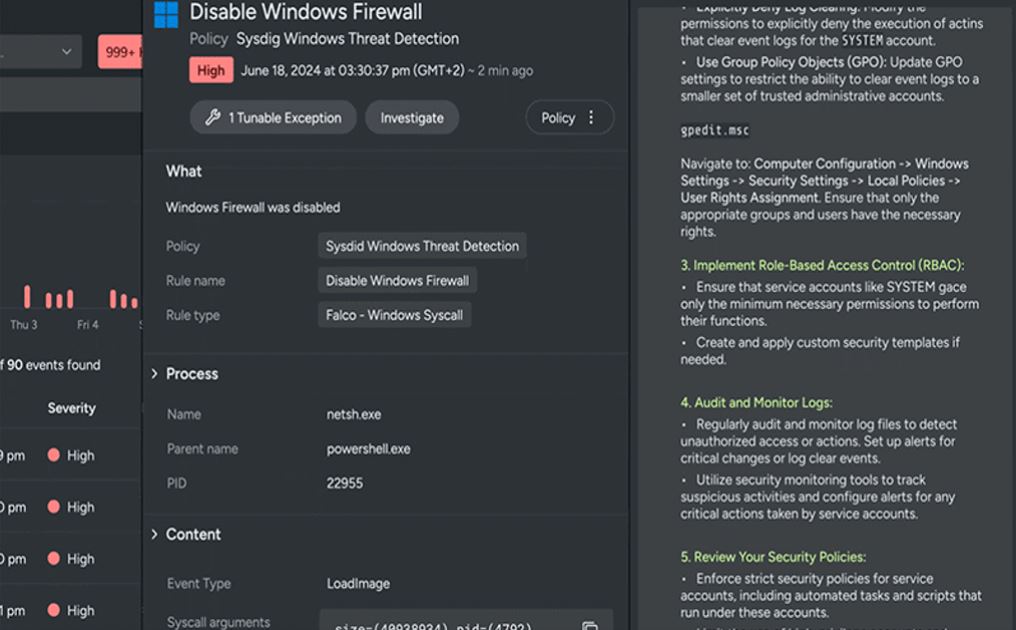
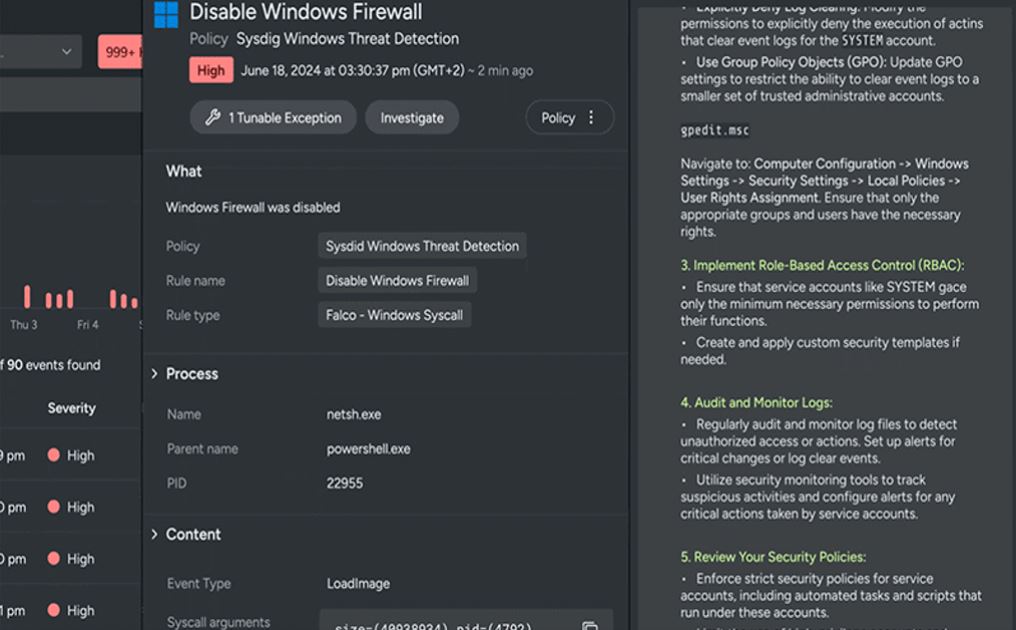
 As cloud environments continue to expand, so do the threats targeting them. In today’s fast-paced digital world, attacks on cloud infrastructure happen within 10 minutes, leaving traditional security tools struggling…
As cloud environments continue to expand, so do the threats targeting them. In today’s fast-paced digital world, attacks on cloud infrastructure happen within 10 minutes, leaving traditional security tools struggling…
The post Spotlight on Sysdig appeared first on Cyber Defense Magazine.