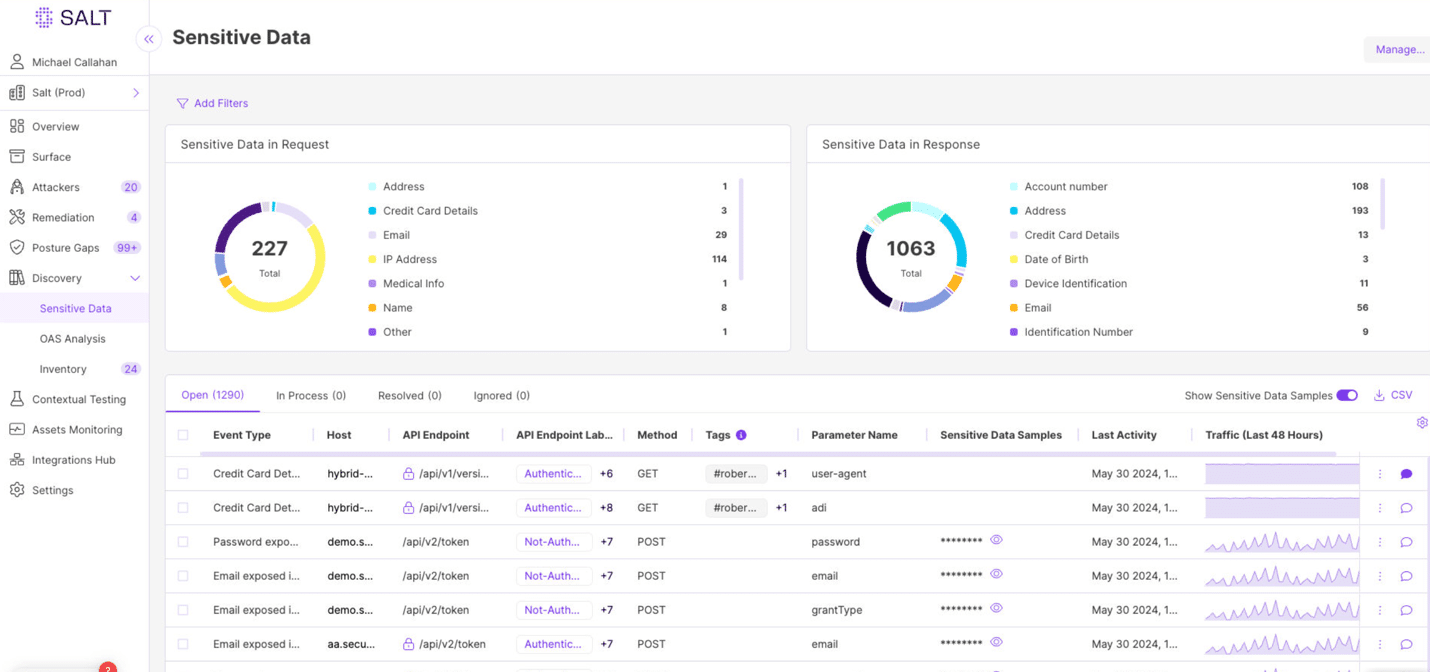
In a world where APIs have become integral to the digital and technical experience, they also represent a significant security risk, often flying under the radar of traditional security solutions….
The post Innovator Spotlight: Salt Security appeared first on Cyber Defense Magazine.