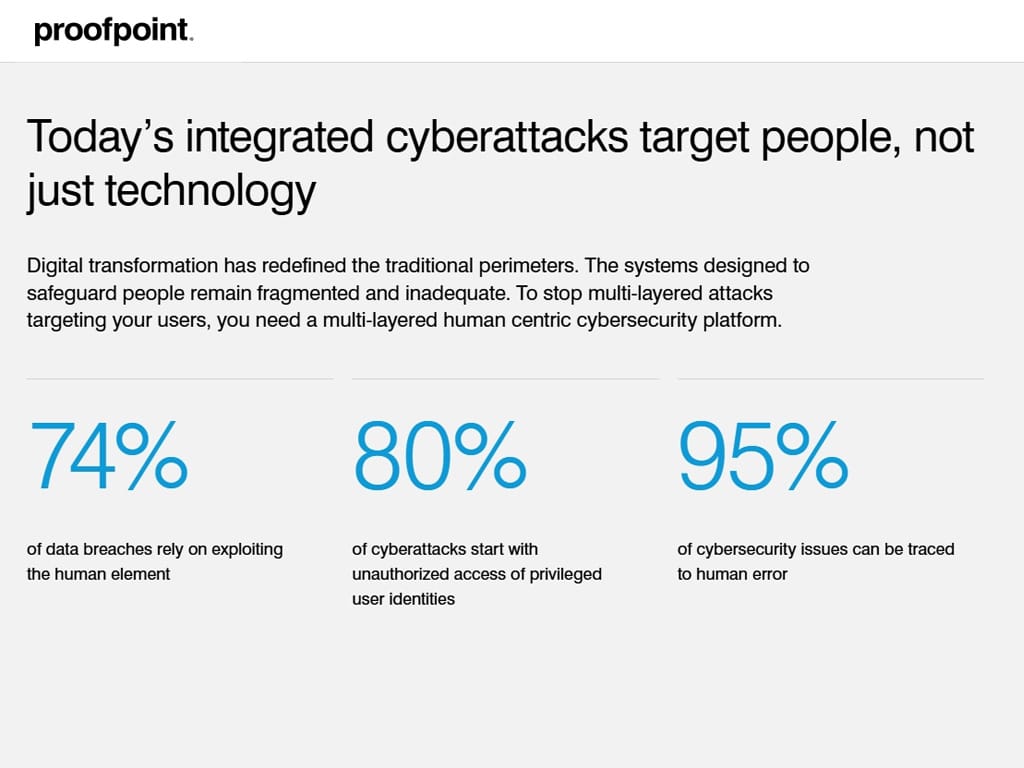
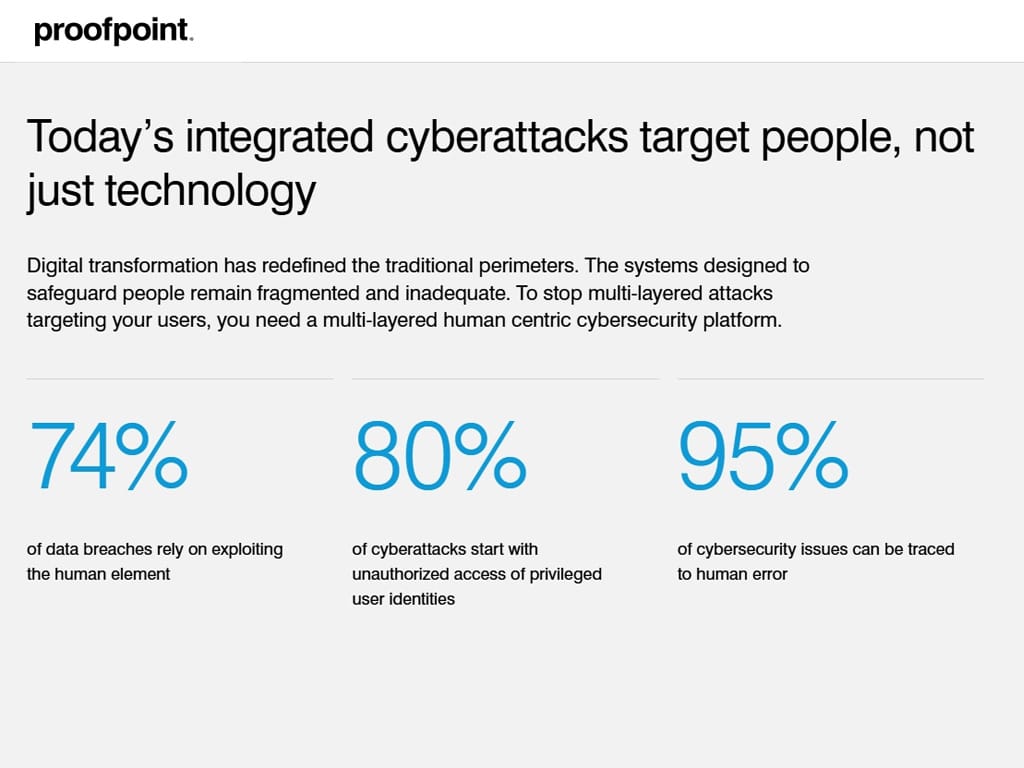
 I was thrilled to catch up with Proofpoint top executives, recently, to discuss Proofpoint’s AI-powered solution and critical issues including data leakage and insider risks. In an era where digital…
I was thrilled to catch up with Proofpoint top executives, recently, to discuss Proofpoint’s AI-powered solution and critical issues including data leakage and insider risks. In an era where digital…
The post Publishers Spotlight: Proofpoint appeared first on Cyber Defense Magazine.


