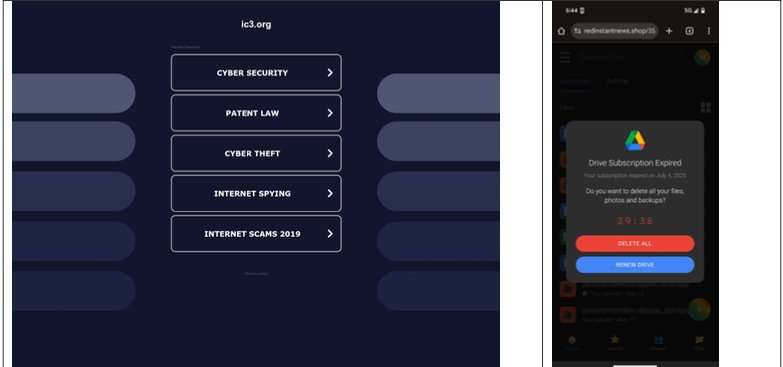
On Friday, July 19, 2024, the world experienced a massive IT outage that disrupted businesses, governments, and other users across the globe. The outage impacted numerous critical services—most notably medical…
On Friday, July 19, 2024, the world experienced a massive IT outage that disrupted businesses, governments, and other users across the globe. The outage impacted numerous critical services—most notably medical…
The post Lessons from the Global IT Outage of July 19, 2024 appeared first on Cyber Defense Magazine.