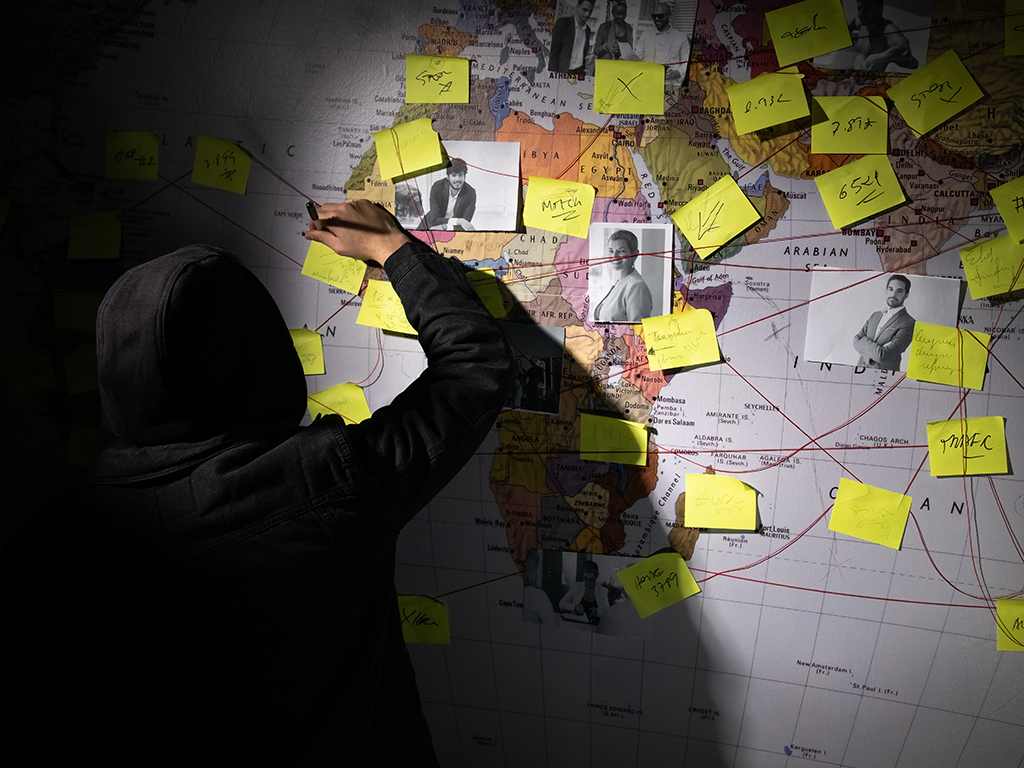
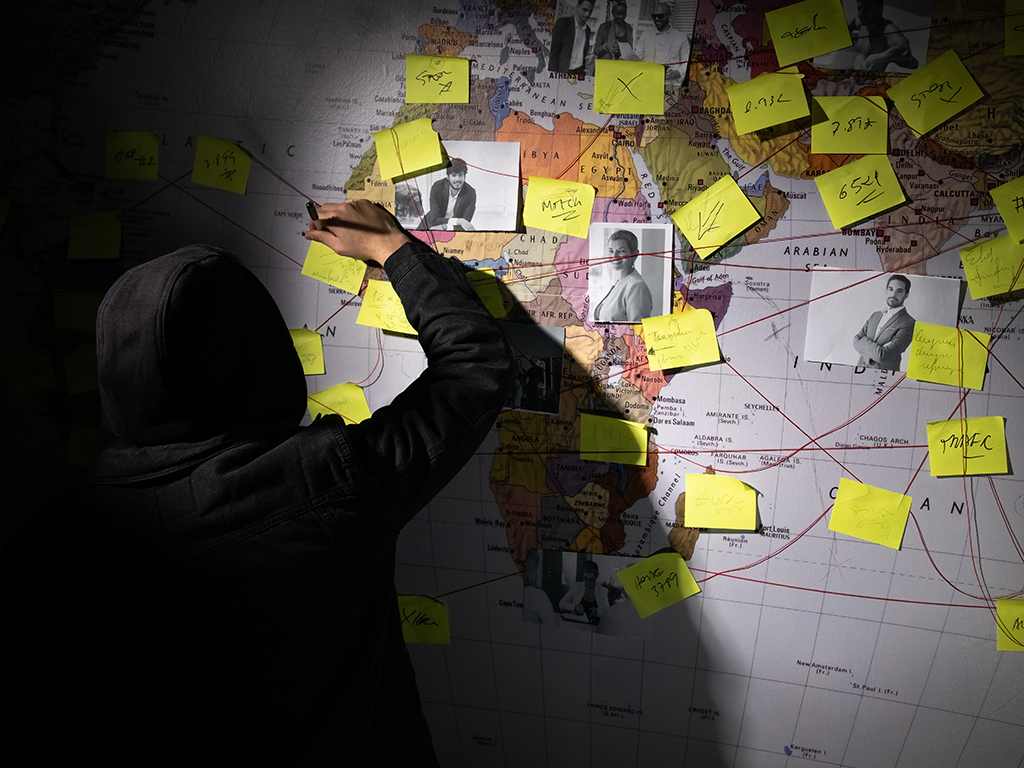
 Only 42% of companies discover breaches through their own security teams. CISOs are often “blind” to third-party security practices and crucial data pipelines. This lack of transparency and reliance on their providers…
Only 42% of companies discover breaches through their own security teams. CISOs are often “blind” to third-party security practices and crucial data pipelines. This lack of transparency and reliance on their providers…
The post How Businesses Can Turn the Expanding Attack Surface into an Opportunity appeared first on Cyber Defense Magazine.
