The post PIM vs PAM vs IAM. Definitions and Roles in the Cybersecurity Strategy appeared first on Heimdal Security Blog.
Related Posts
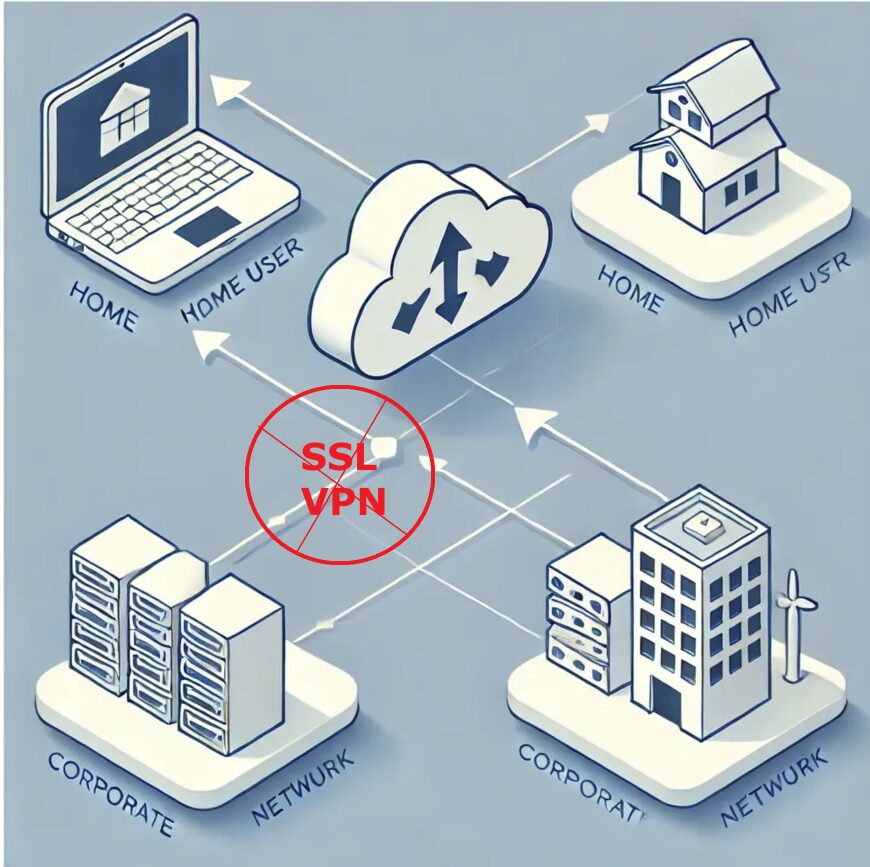
Urgent advisory on the Fortigate SSL VPN breach: Learn how…
- rooter
- January 27, 2025
- 5 min read
- 0
Bridging the Gap Between Cyber Innovation and Regulated Markets Addressing…
- rooter
- January 14, 2025
- 1 min read
- 0
EXECUTIVE SUMMARY: Cyber criminals are increasing their use of zero-day…
- rooter
- October 9, 2023
- 4 min read
- 0
by Gary S. Miliefsky, CISSP, fmDHS Ho-ho-hold on to your…
- rooter
- December 6, 2024
- 1 min read
- 0