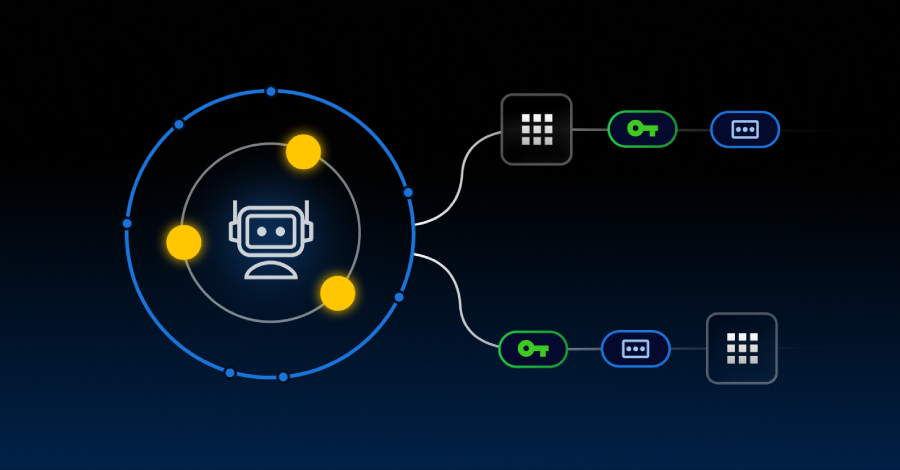
The cybersecurity world is on the brink of a revolution, driven by quantum computing. Quantum computers can also break the encryption systems we depend on daily while powering breakthroughs in…
The cybersecurity world is on the brink of a revolution, driven by quantum computing. Quantum computers can also break the encryption systems we depend on daily while powering breakthroughs in…
The post Zero-Trust Architecture in the Era of Quantum Computing: A Proactive Defense Strategy appeared first on Cyber Defense Magazine.