By Jeremy Butteriss, EGM Ecosystem and Partnerships, Xero An iconic moment in the rise of ecosystems was Steve Ballmer on stage saying ‘developers, developers, developers’ at the 1999 Microsoft .NET […]
By Jeremy Butteriss, EGM Ecosystem and Partnerships, Xero An iconic moment in the rise of ecosystems was Steve Ballmer on stage saying ‘developers, developers, developers’ at the 1999 Microsoft .NET […]
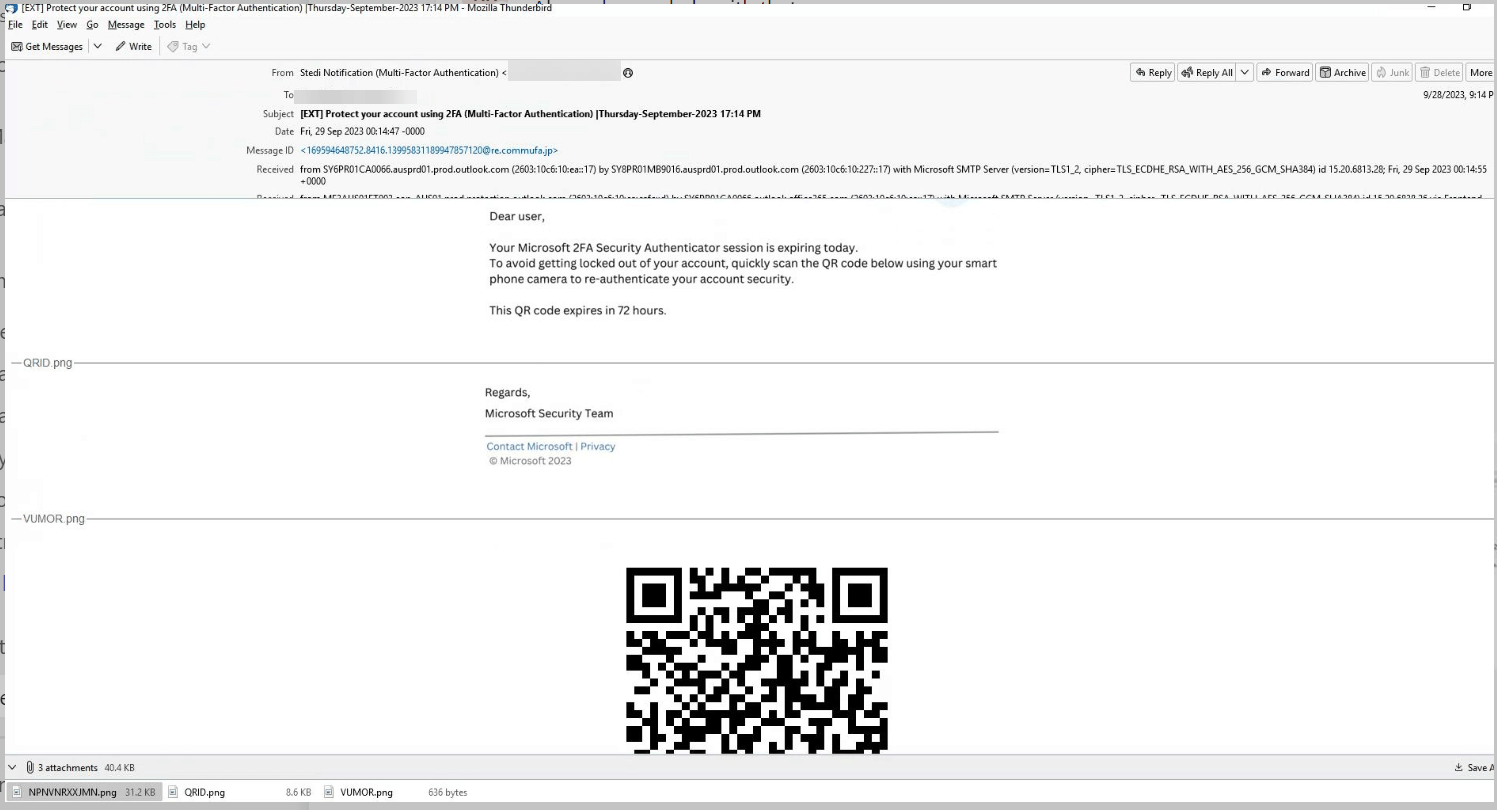
The post Building For a More Secure Future: How Developers Can Prioritize Cybersecurity appeared first on Cyber Defense Magazine.