To address the ever-evolving cybersecurity landscape and equip organizations with information and resources to more quickly and effectively manage cybersecurity risk and improve their cybersecurity posture, NIST published a significant update to the
Related Posts
We can strip attackers of their power by implementing layered…
- rooter
- August 20, 2025
- 1 min read
- 0
Cybersecurity in manufacturing businesses is unique. The sector faces several…
- rooter
- August 6, 2025
- 1 min read
- 0
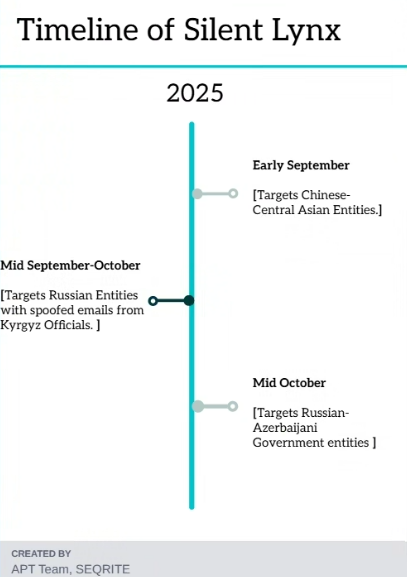
Introduction Timeline Key Targets. Industries Affecte d. Geographical Focus.…
- rooter
- November 3, 2025
- 22 min read
- 0