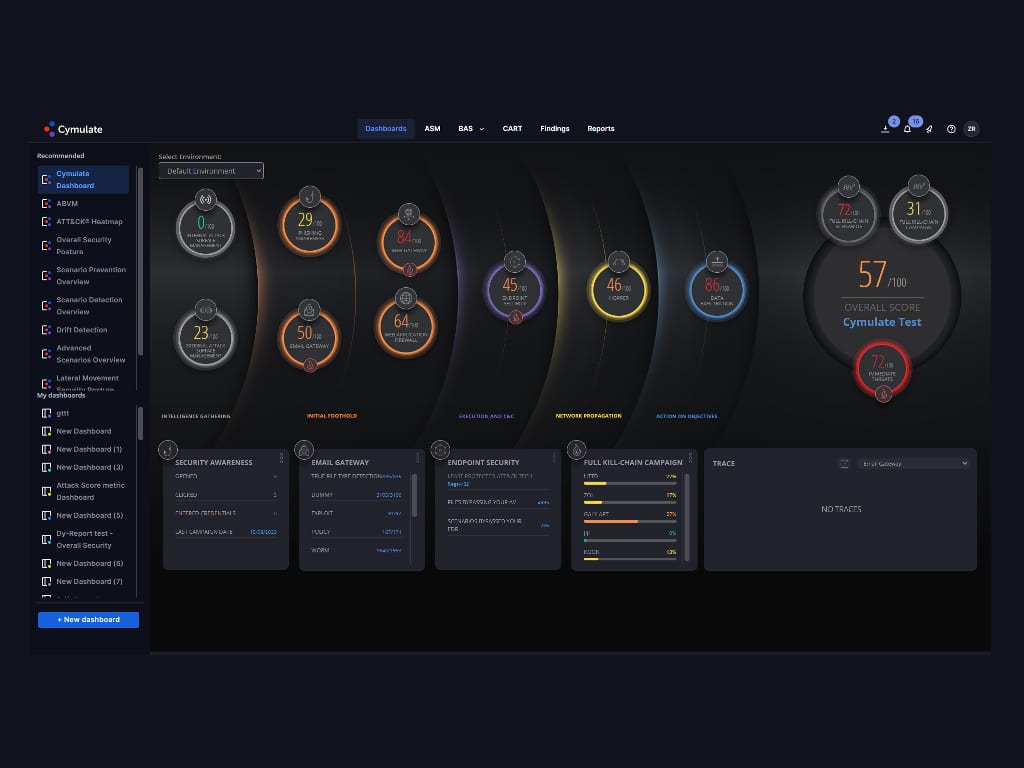
Today, cloud environments are more complex than ever. Organizations are navigating multicloud, multi-tenant, multi-national, and multi-business unit landscapes. On top of this, the speed of fluctuation in usage and cloud…
Today, cloud environments are more complex than ever. Organizations are navigating multicloud, multi-tenant, multi-national, and multi-business unit landscapes. On top of this, the speed of fluctuation in usage and cloud…
The post How To Leverage Cloud Analytics to Detect and Prevent Cybersecurity Threats in Real-Time appeared first on Cyber Defense Magazine.