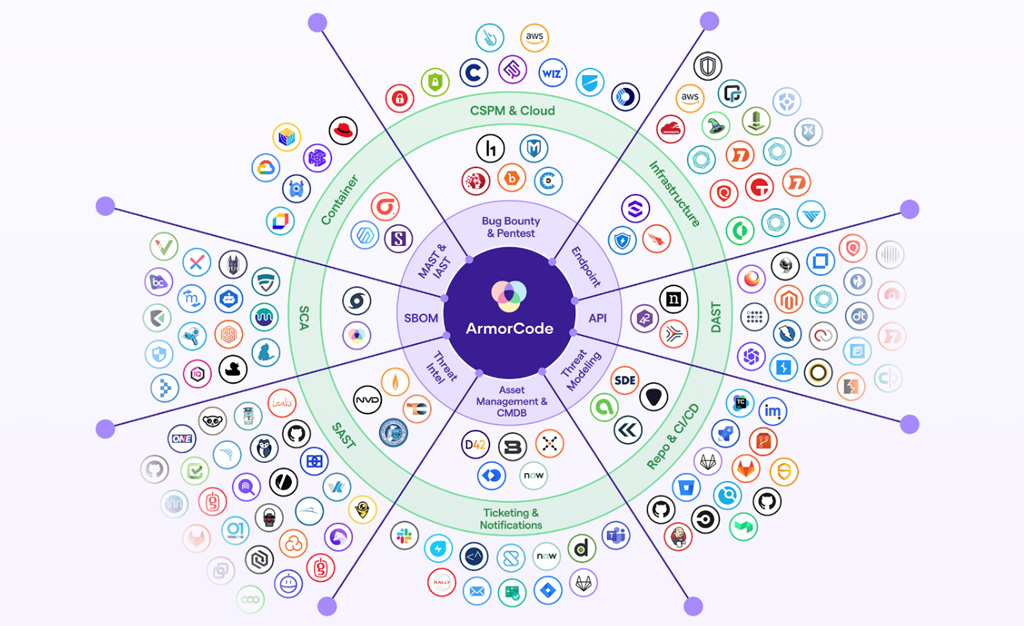
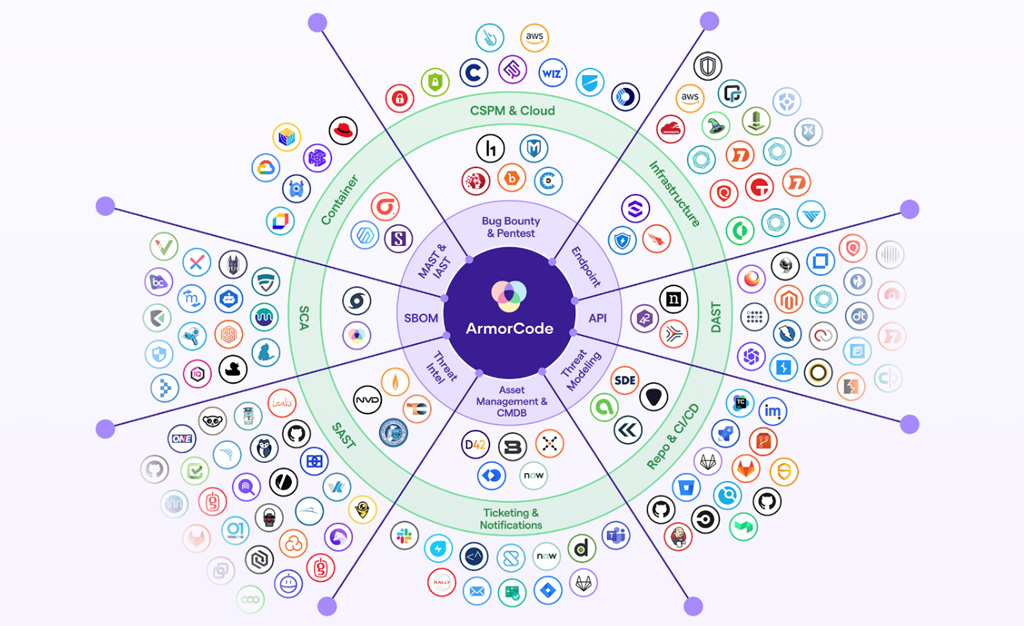
 As the world of software development accelerates, the need to secure applications from the earliest stages of development has become critical. The rise of DevSecOps has placed immense pressure on…
As the world of software development accelerates, the need to secure applications from the earliest stages of development has become critical. The rise of DevSecOps has placed immense pressure on…
The post Innovator Spotlight: ArmorCode appeared first on Cyber Defense Magazine.
