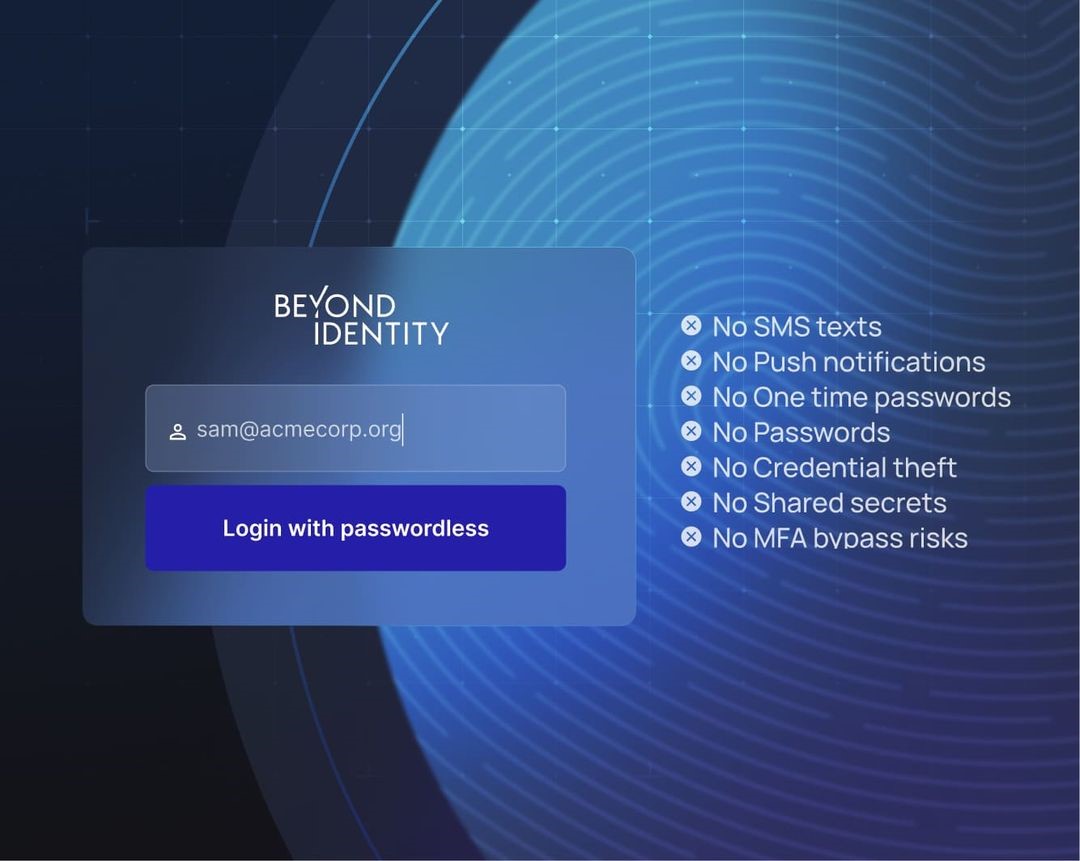
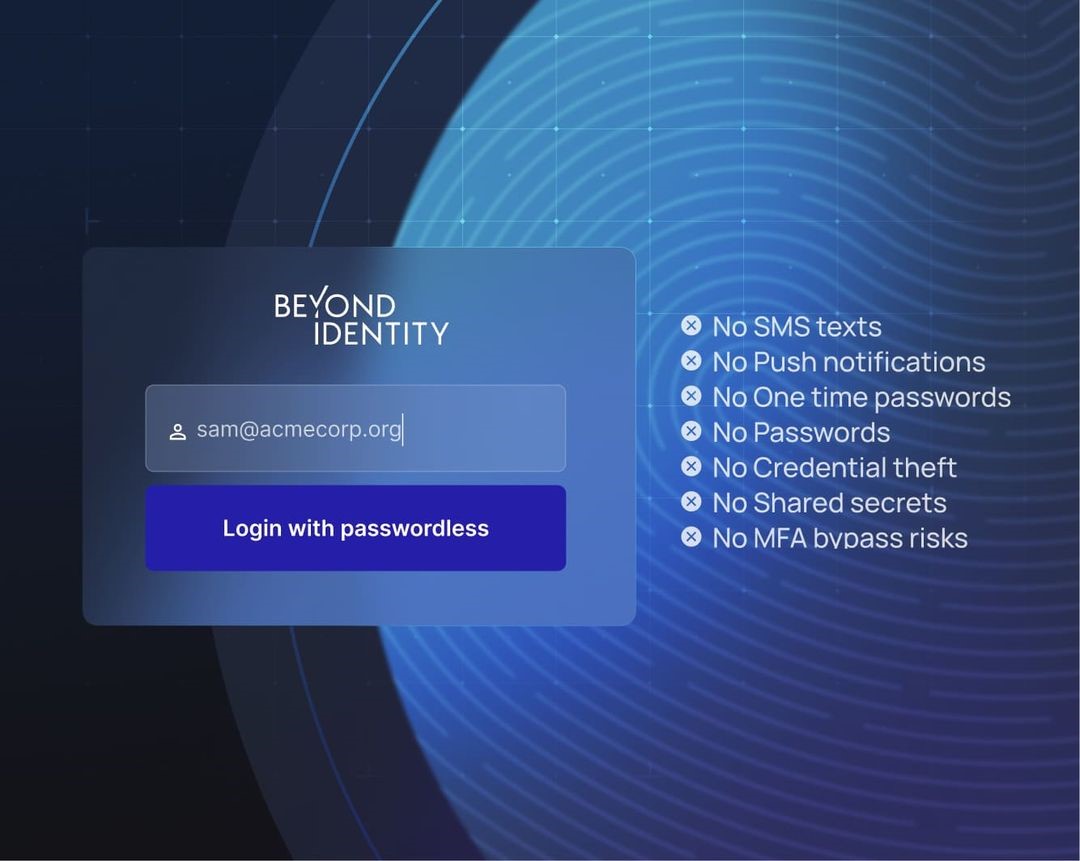
 At Black Hat 2024, I had the opportunity to speak with Jasson Casey, CEO of Beyond Identity, about their groundbreaking work in secure identity and access management (IAM). In an…
At Black Hat 2024, I had the opportunity to speak with Jasson Casey, CEO of Beyond Identity, about their groundbreaking work in secure identity and access management (IAM). In an…
The post Innovator Spotlight: Beyond Identity appeared first on Cyber Defense Magazine.


