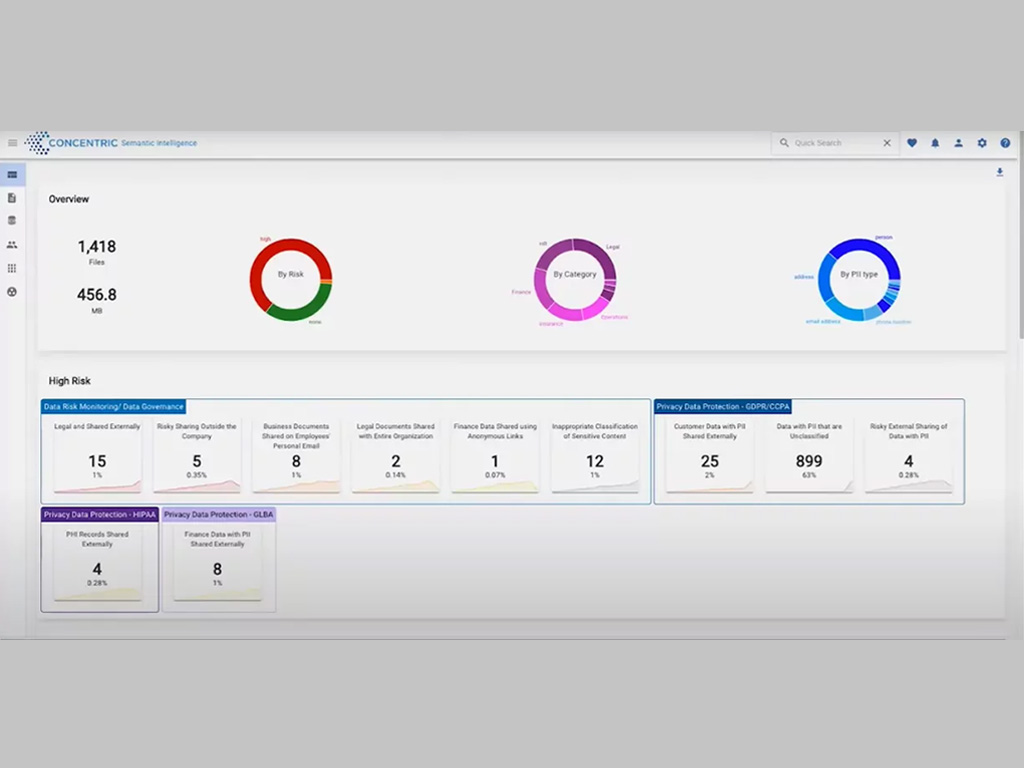
It’s not enough for companies to just discover and monitor sensitive data. They need tools that can proactively fix any security issues to prevent data loss and meet compliance standards….
The post Innovator Spotlight: Concentric AI appeared first on Cyber Defense Magazine.