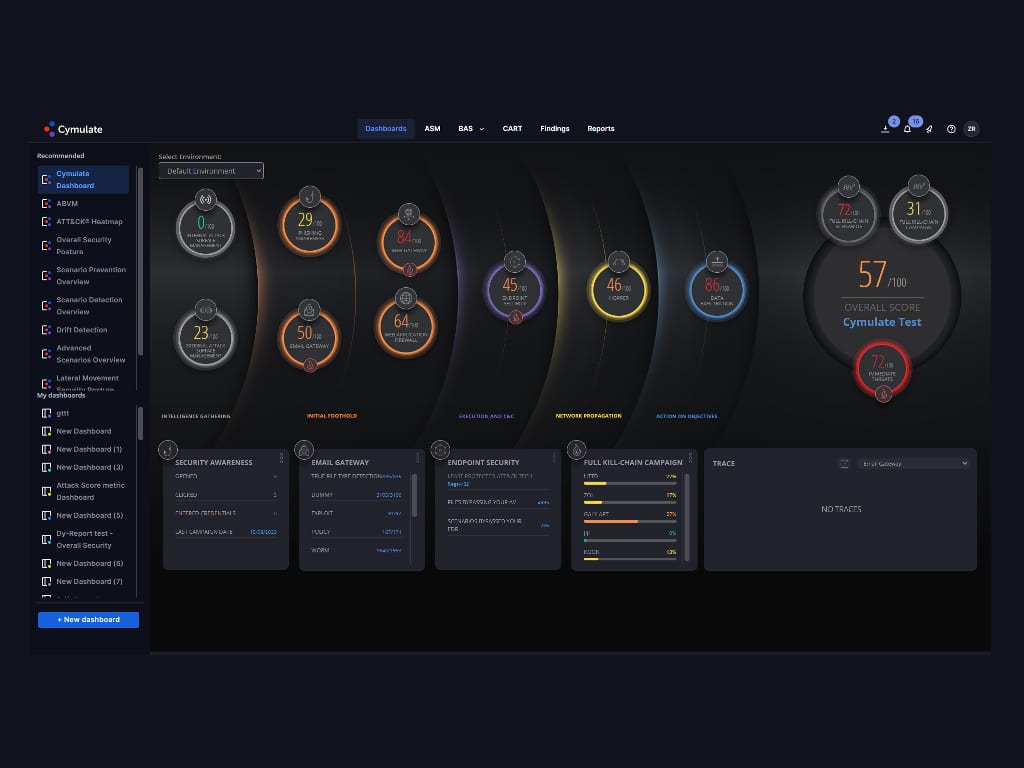
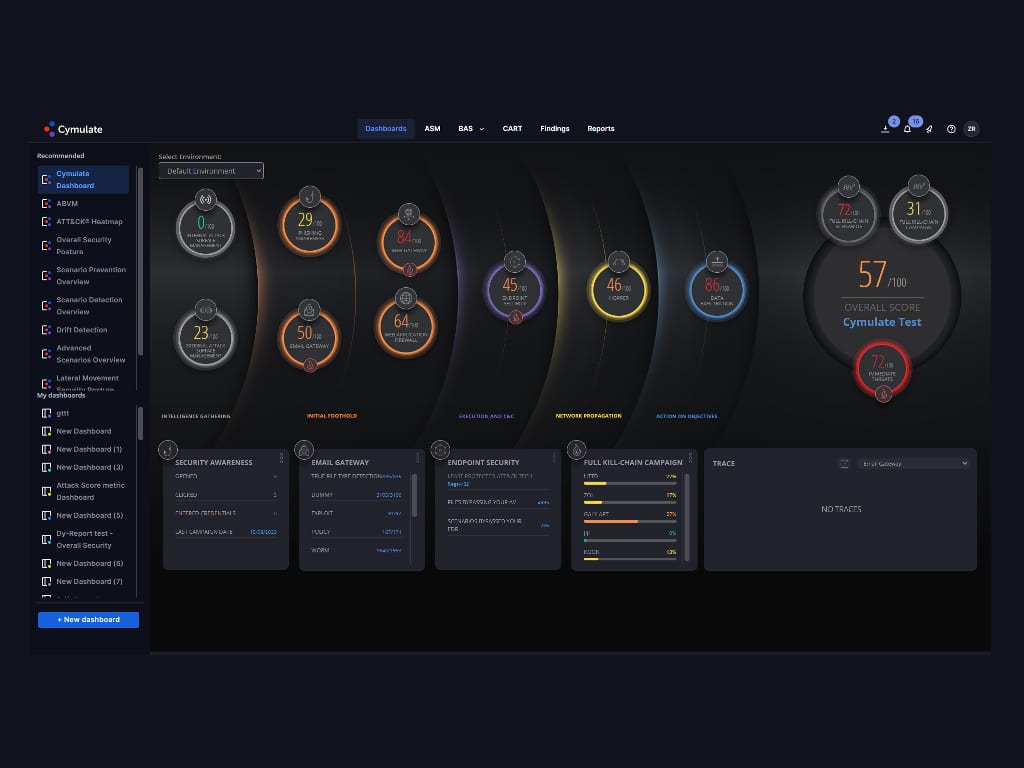
 AI Copilot: Revolutionizing Threat Exposure Validation by Samridhi Agarwal, Master’s Student, CMU During BlackHat, Cymulate, a leader in security and exposure validation, has officially launched Cymulate AI Copilot, an innovative,…
AI Copilot: Revolutionizing Threat Exposure Validation by Samridhi Agarwal, Master’s Student, CMU During BlackHat, Cymulate, a leader in security and exposure validation, has officially launched Cymulate AI Copilot, an innovative,…
The post Innovator Spotlight: Cymulate appeared first on Cyber Defense Magazine.



