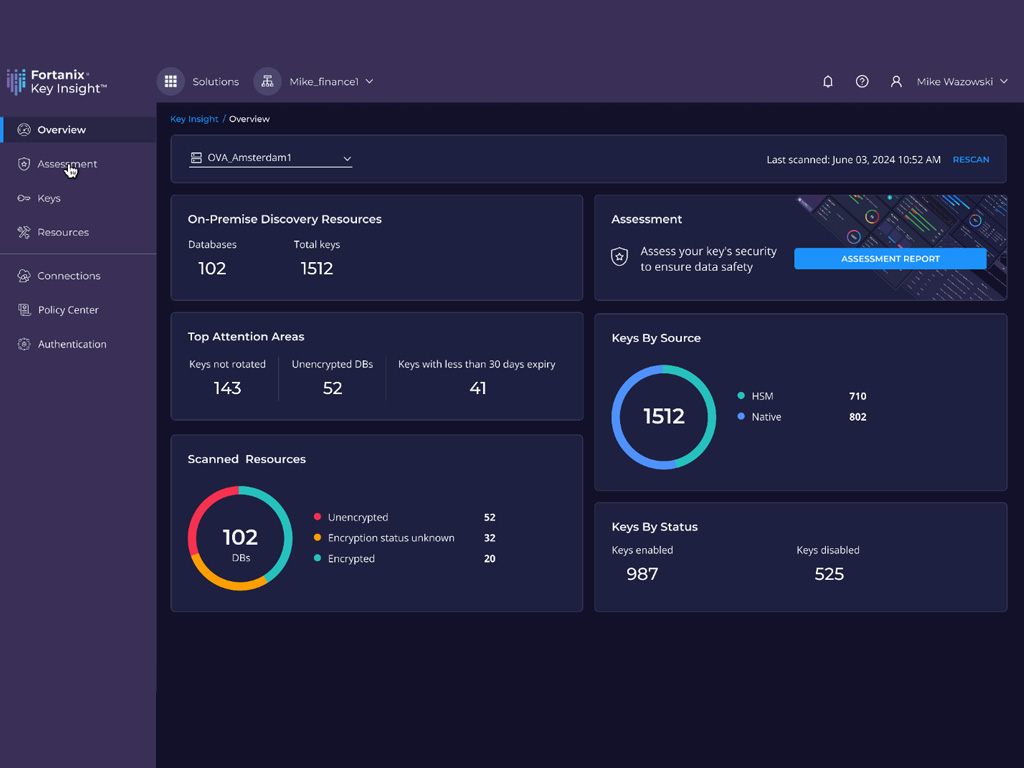
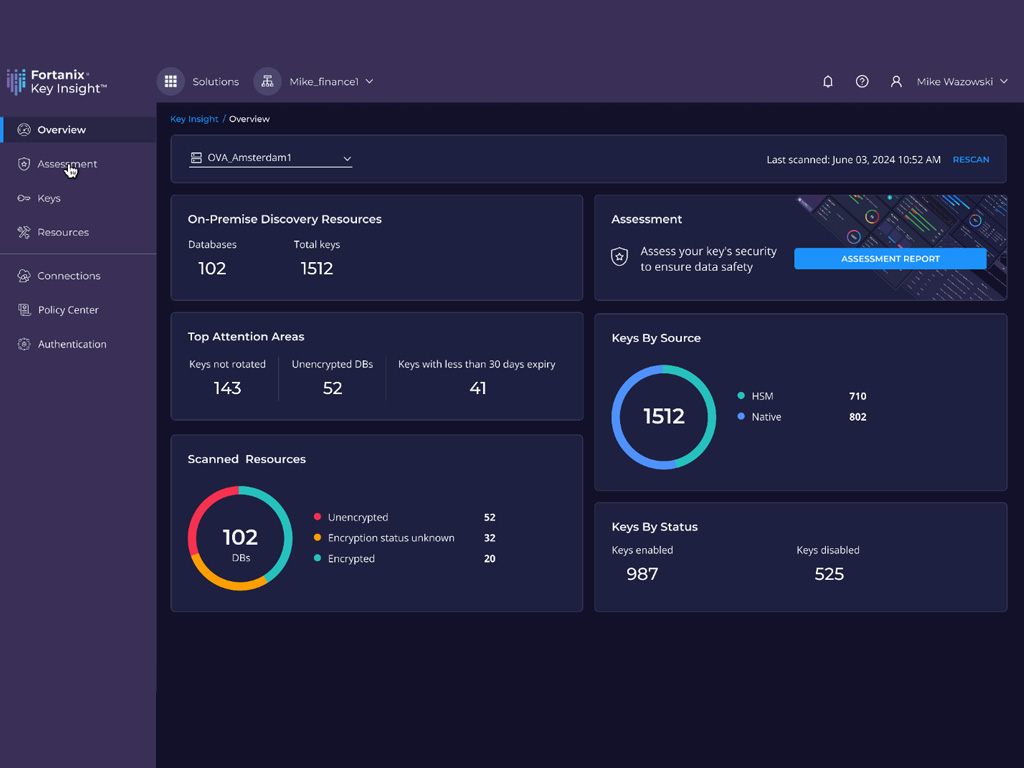
 Unveiling Secure Data Practices in a World of AI Risks by Samridhi Agarwal, Master’s Student, CMU In an era where artificial intelligence is becoming increasingly prevalent, organizations face new and…
Unveiling Secure Data Practices in a World of AI Risks by Samridhi Agarwal, Master’s Student, CMU In an era where artificial intelligence is becoming increasingly prevalent, organizations face new and…
The post Innovator Spotlight: Fortanix appeared first on Cyber Defense Magazine.