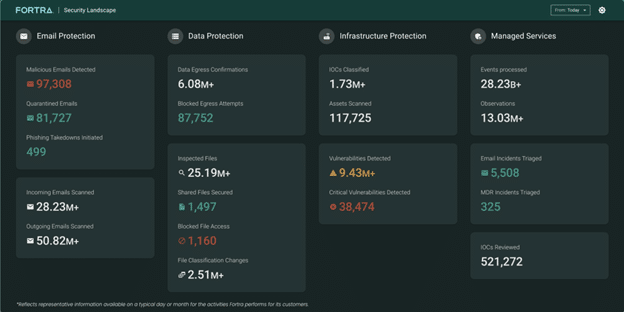
 by Dan K. Anderson CEO, CISO, and vCISO As cyber threats grow more sophisticated and frequent, organizations face immense pressure to simplify their security stacks and improve operational efficiency. According…
by Dan K. Anderson CEO, CISO, and vCISO As cyber threats grow more sophisticated and frequent, organizations face immense pressure to simplify their security stacks and improve operational efficiency. According…
The post Innovator Spotlight: Fortra appeared first on Cyber Defense Magazine.