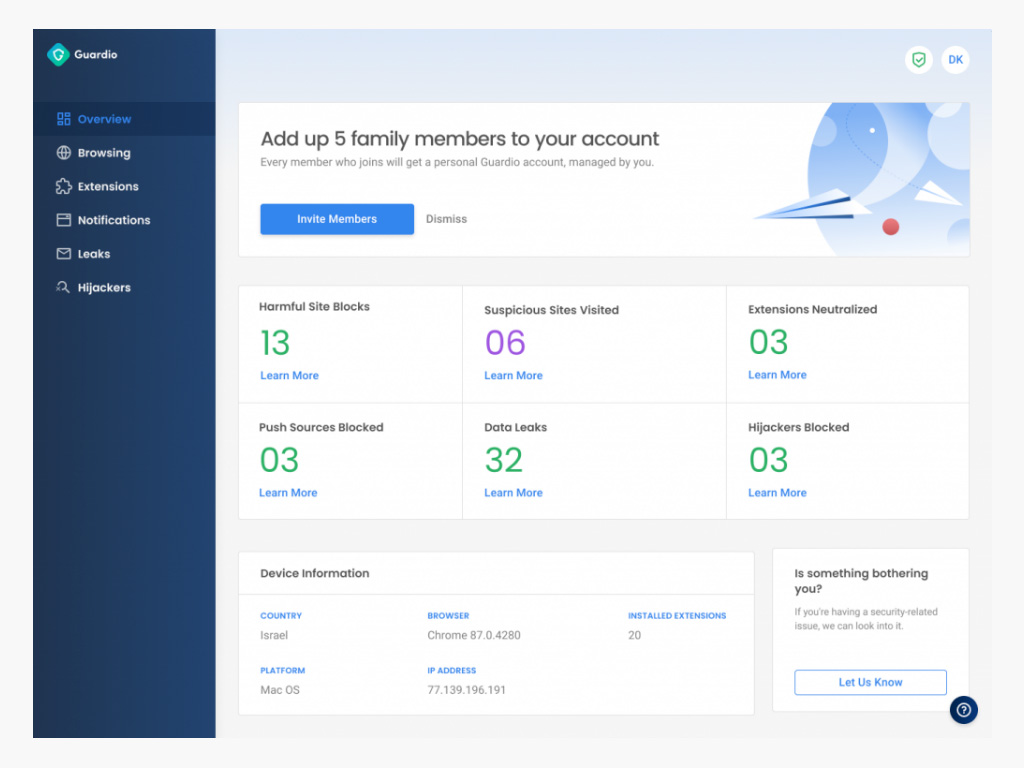
Cyber threats are becoming more sophisticated, putting both individuals and businesses at significant risk. The rise in phishing attacks, identity theft, and online fraud highlights the urgent need for accessible…
The post Innovator Spotlight: Guardio appeared first on Cyber Defense Magazine.