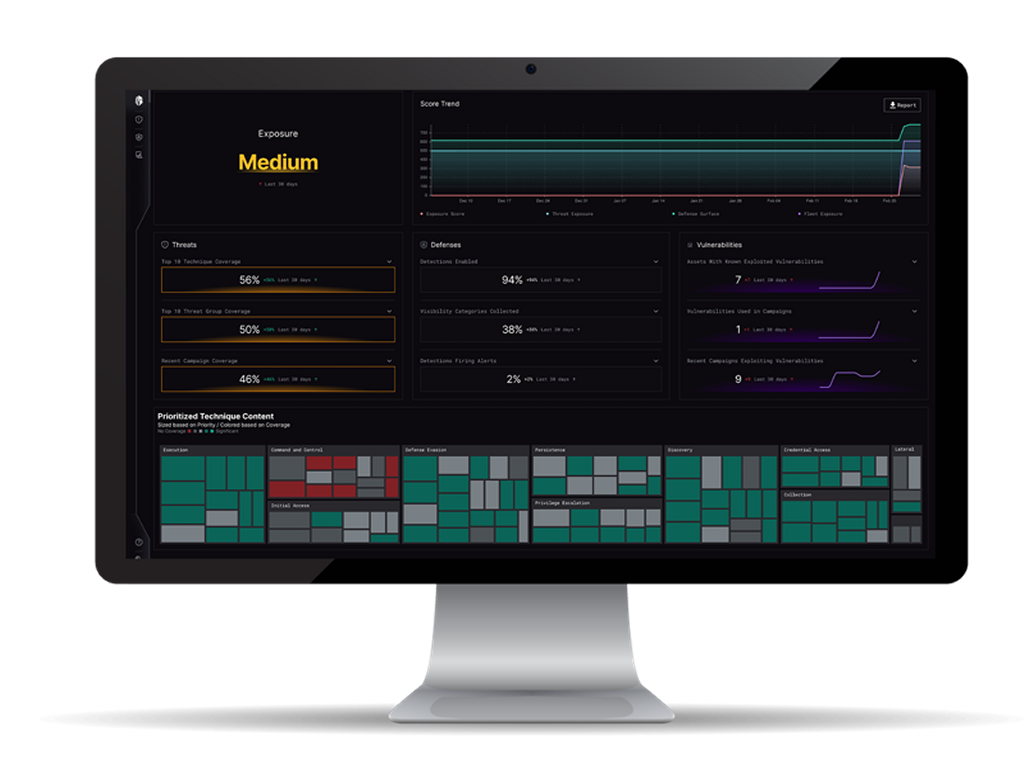
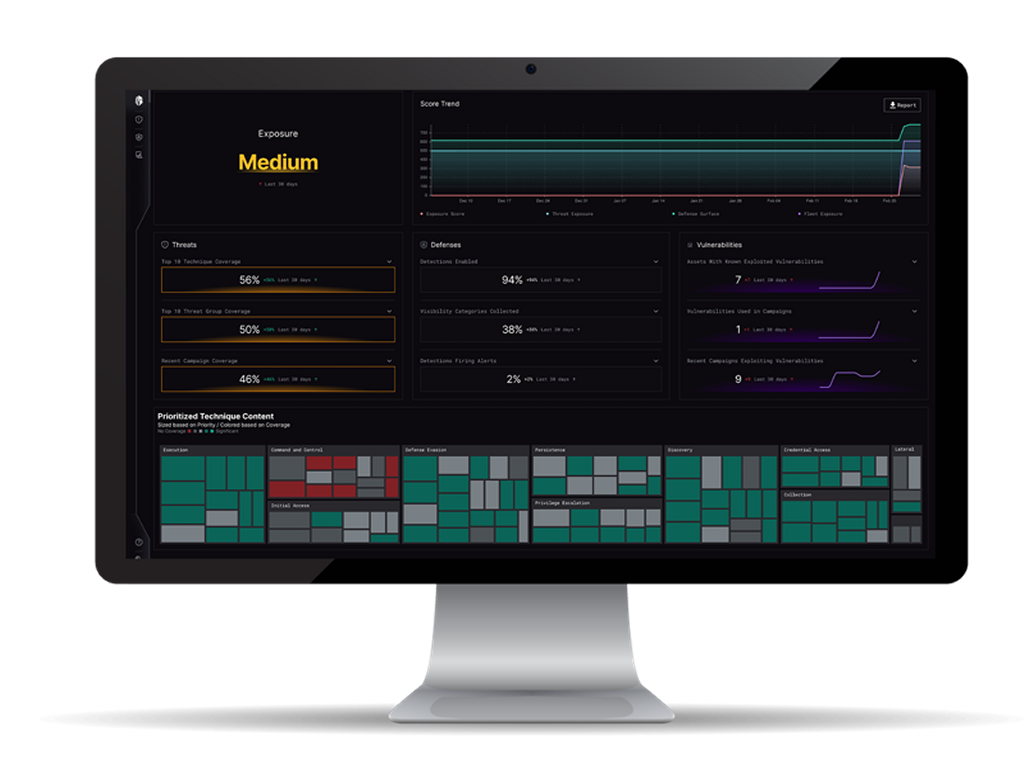
 In the current cybersecurity landscape, the focus has shifted from merely managing vulnerabilities to strategically orchestrating defenses against targeted threats. Organizations are increasingly struggling to optimize their security posture amidst…
In the current cybersecurity landscape, the focus has shifted from merely managing vulnerabilities to strategically orchestrating defenses against targeted threats. Organizations are increasingly struggling to optimize their security posture amidst…
The post Innovator Spotlight: Interpres Security appeared first on Cyber Defense Magazine.

