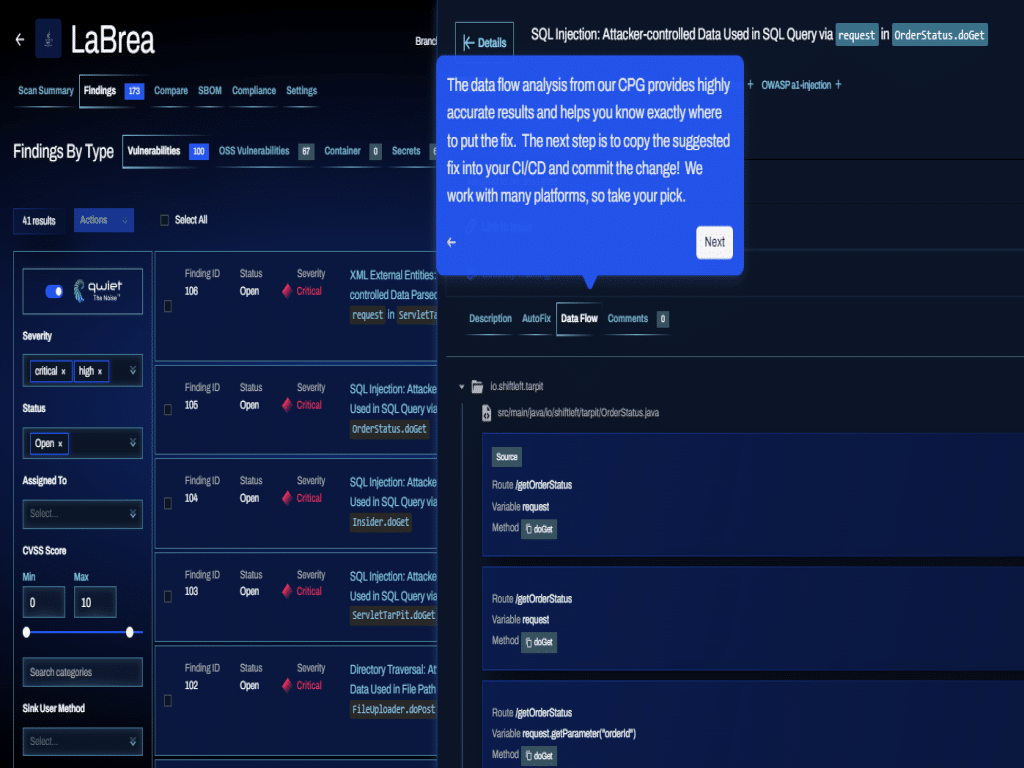
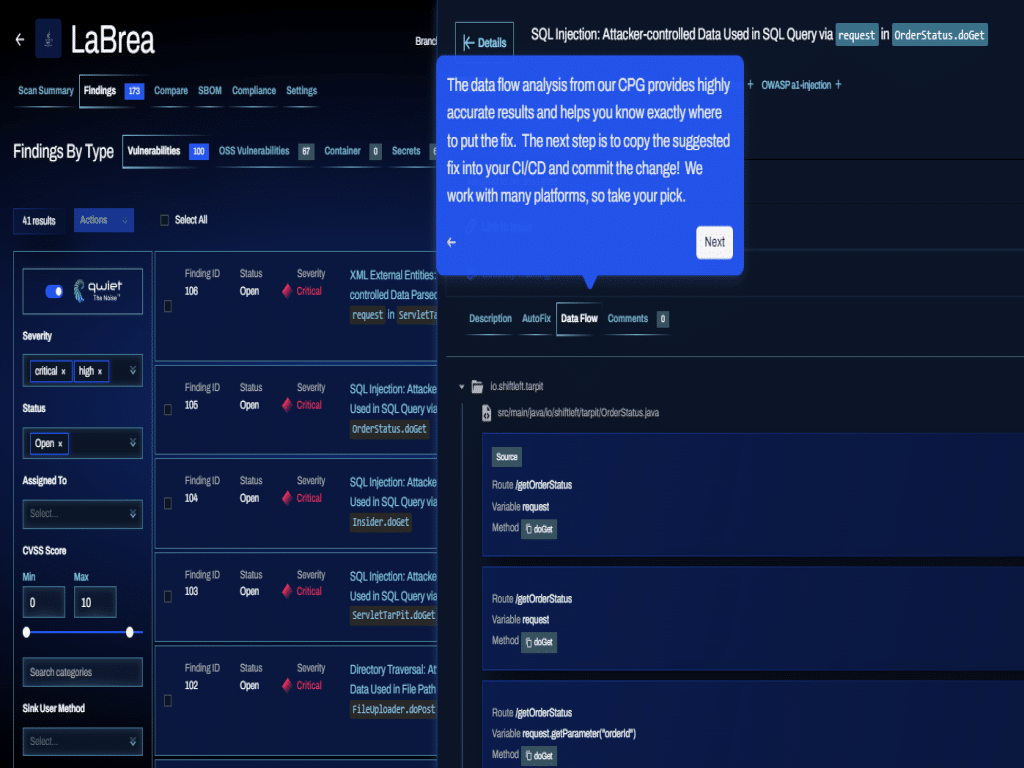
 The volume of code needed is greater than ever while cycles to produce said code are shrinking. One of the consequences of this is security has become secondary – both…
The volume of code needed is greater than ever while cycles to produce said code are shrinking. One of the consequences of this is security has become secondary – both…
The post Innovator Spotlight: Qwiet appeared first on Cyber Defense Magazine.
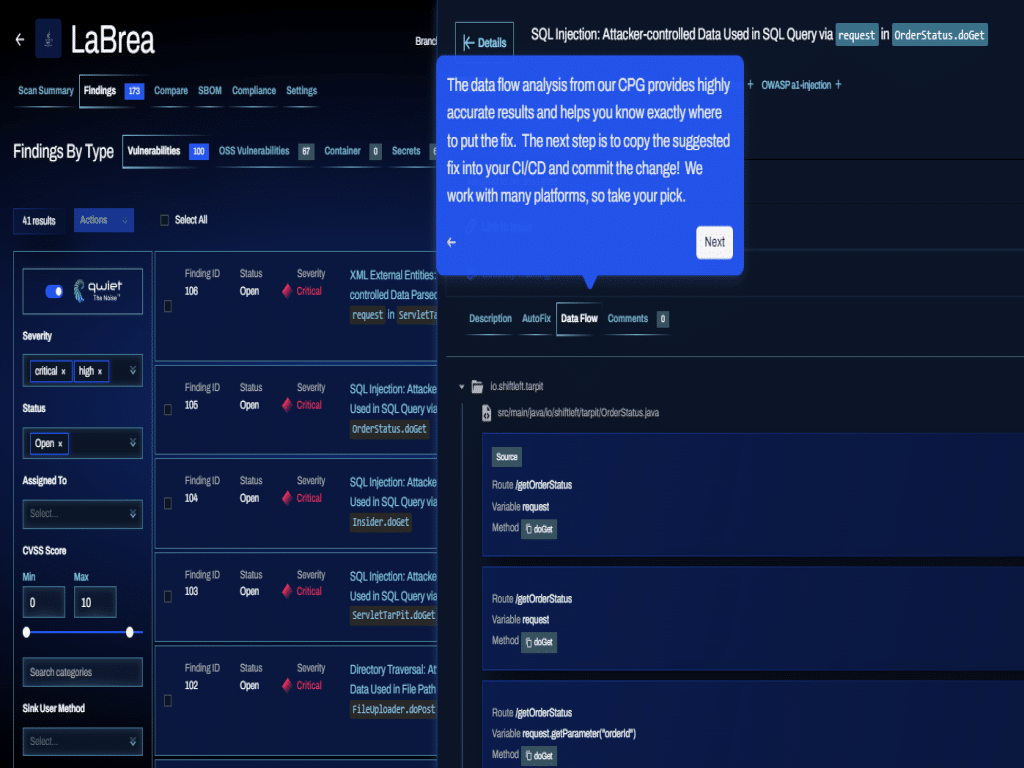
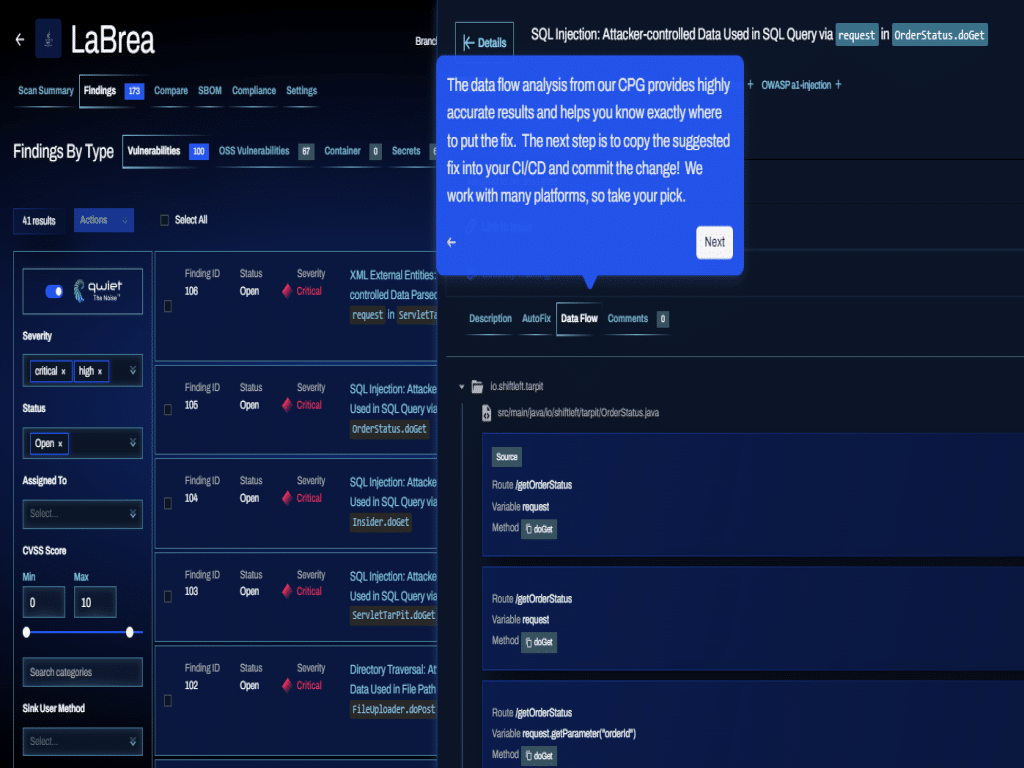
 The volume of code needed is greater than ever while cycles to produce said code are shrinking. One of the consequences of this is security has become secondary – both…
The volume of code needed is greater than ever while cycles to produce said code are shrinking. One of the consequences of this is security has become secondary – both…
The post Innovator Spotlight: Qwiet appeared first on Cyber Defense Magazine.