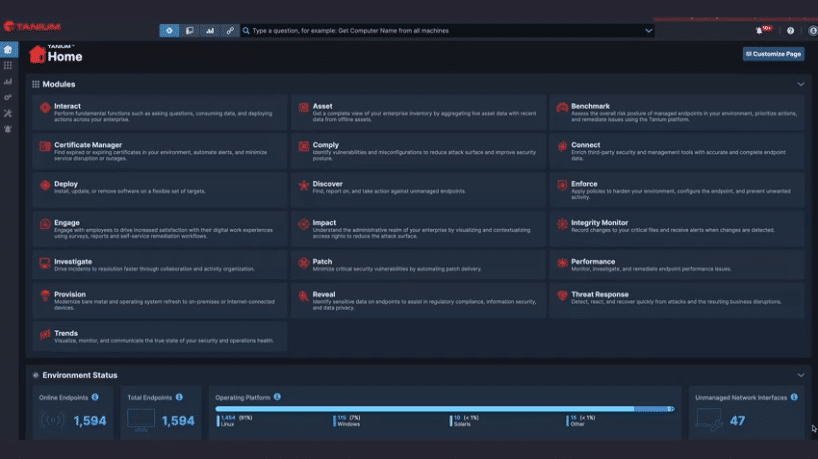
During my conversation with Melissa Bischoping, Senior Director of Security & Product Design Research at Tanium, she emphasized how the company addresses the critical challenge of operational risk and security…
The post Innovator Spotlight: Tanium appeared first on Cyber Defense Magazine.