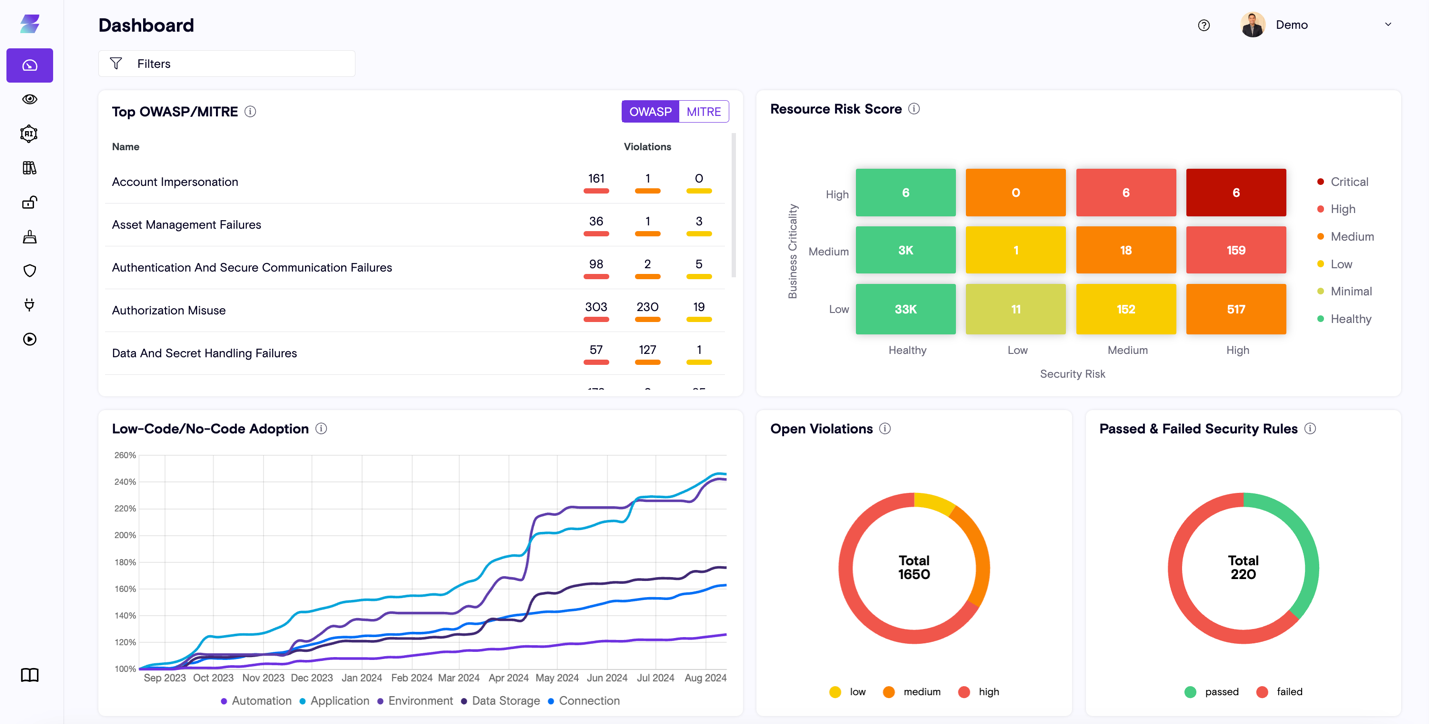
 Another innovative industry leader I had the pleasure of speaking with was Michael Bargury, Co-Founder and CTO of Zenity, a pioneering company that is redefining how enterprises approach security for…
Another innovative industry leader I had the pleasure of speaking with was Michael Bargury, Co-Founder and CTO of Zenity, a pioneering company that is redefining how enterprises approach security for…
The post Innovator Spotlight: Zenity appeared first on Cyber Defense Magazine.