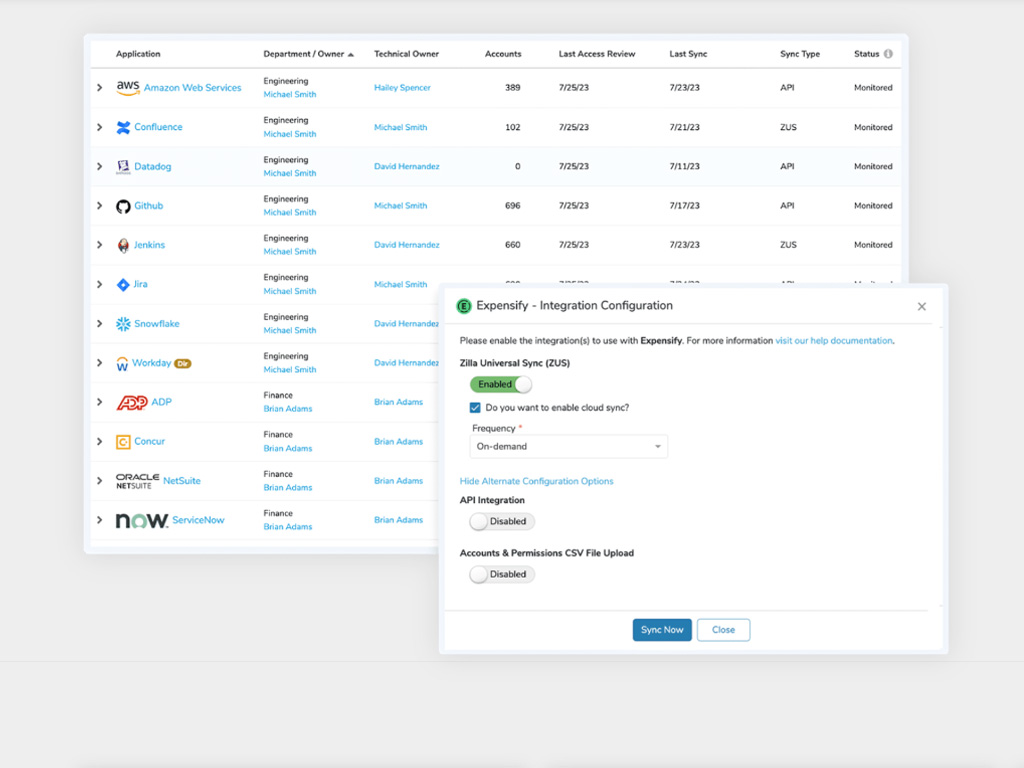
 by Dan K. Anderson CEO, CISO, and vCISO As organizations grow, managing access to critical systems and ensuring compliance with identity governance and administration (IGA) standards becomes increasingly complex. A…
by Dan K. Anderson CEO, CISO, and vCISO As organizations grow, managing access to critical systems and ensuring compliance with identity governance and administration (IGA) standards becomes increasingly complex. A…
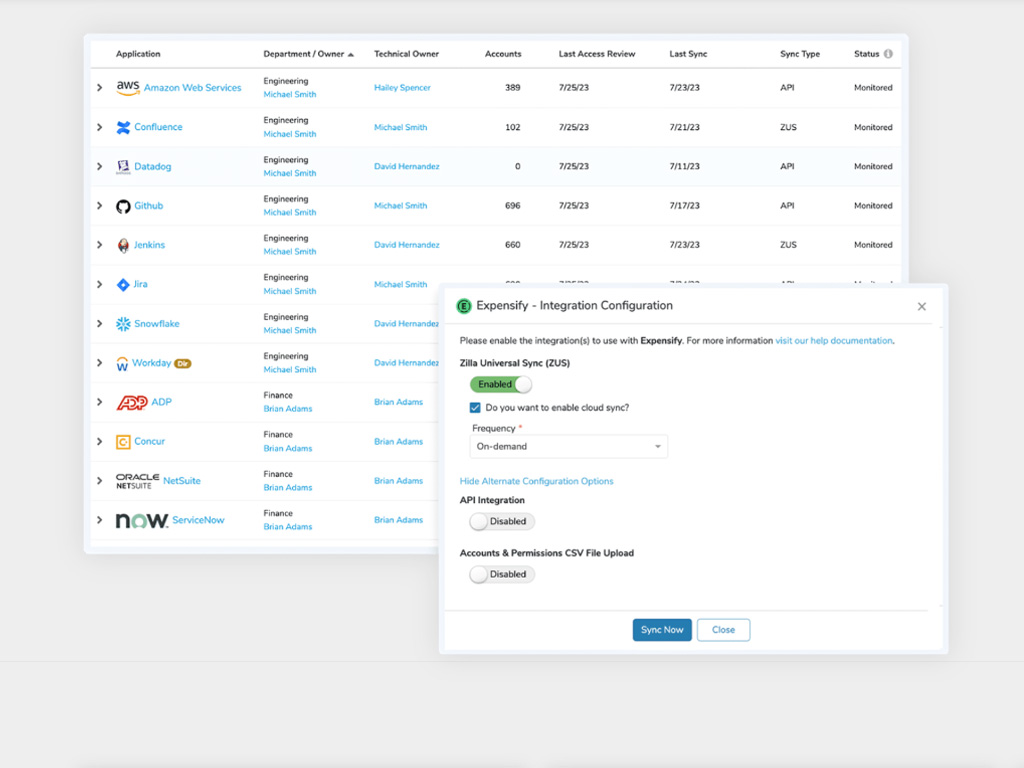
The post Innovator Spotlight: Zilla Security appeared first on Cyber Defense Magazine.