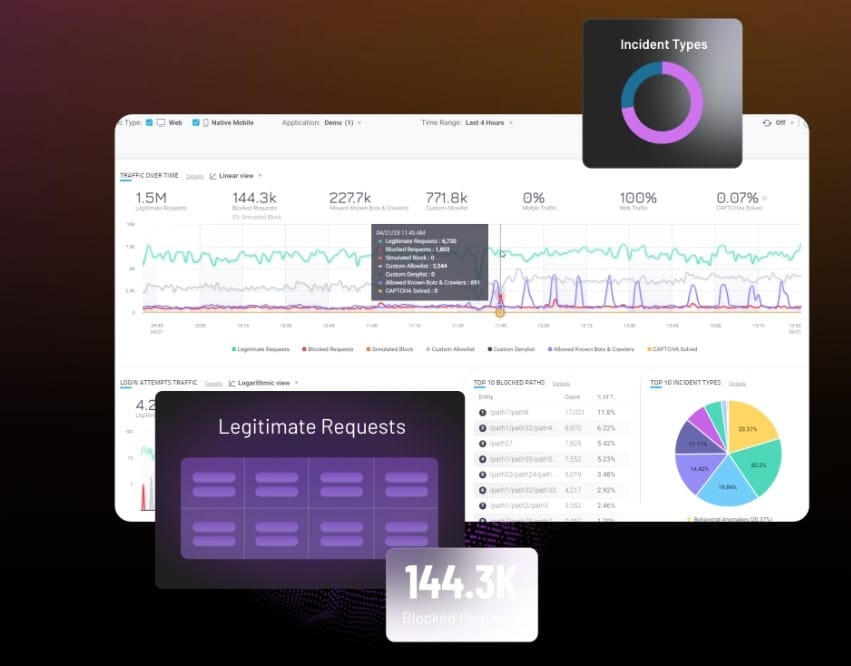
Cybersecurity is the cornerstone of organizational stability and resilience today. Despite its critical importance, budgetary allocations often fall short due to competing priorities. Mimecast recently surveyed 1,100 CISOs and information…
The post Maximizing Cybersecurity Impact Within Budget Constraints appeared first on Cyber Defense Magazine.