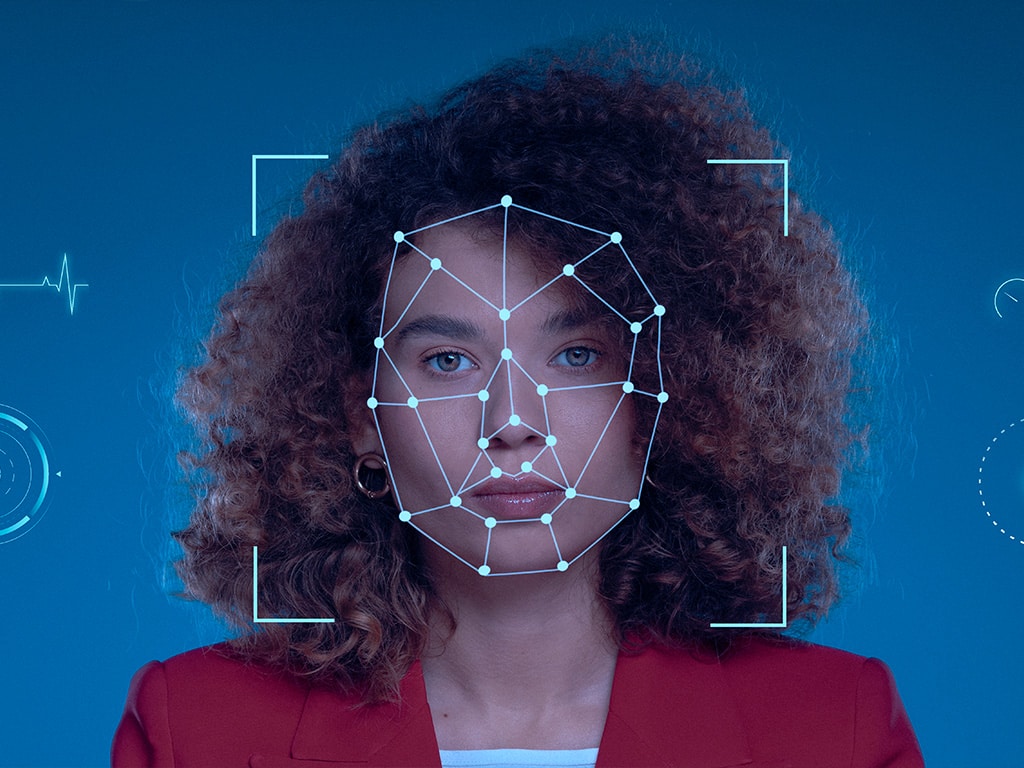
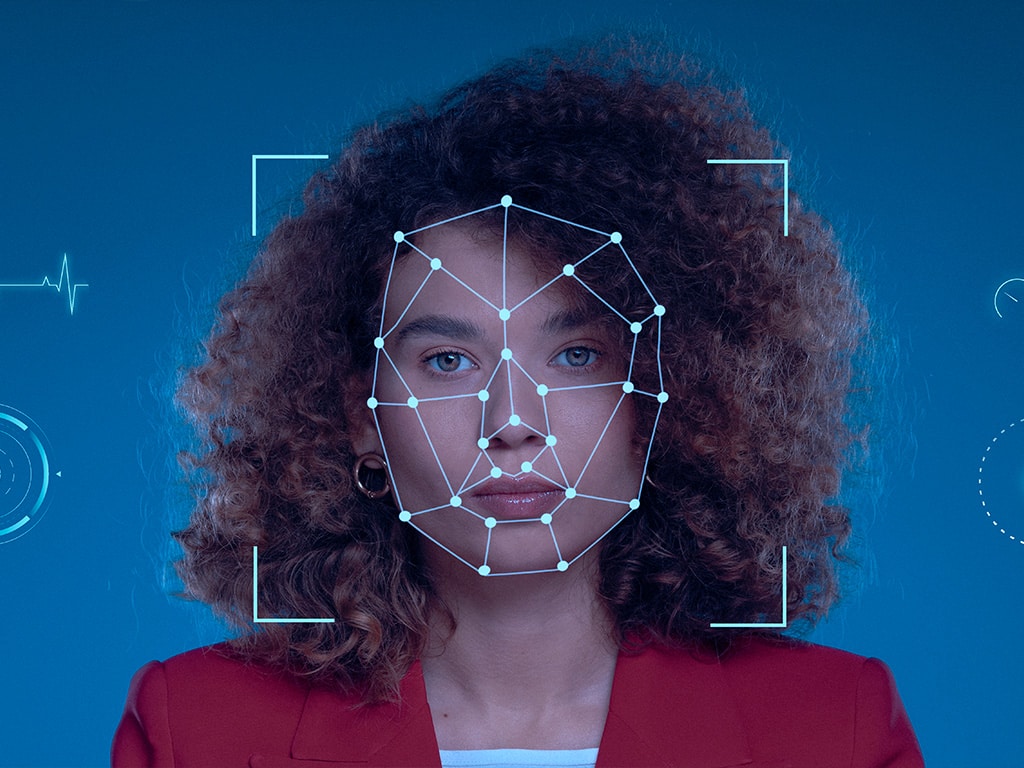
 Federal agencies face a pivotal cybersecurity challenge: prevent unauthorized entities from accessing systems and facilities, while granting authorized federal employees and contractors access commensurate with verified need. Two factors complicate…
Federal agencies face a pivotal cybersecurity challenge: prevent unauthorized entities from accessing systems and facilities, while granting authorized federal employees and contractors access commensurate with verified need. Two factors complicate…
The post NextGen Identity Management appeared first on Cyber Defense Magazine.


