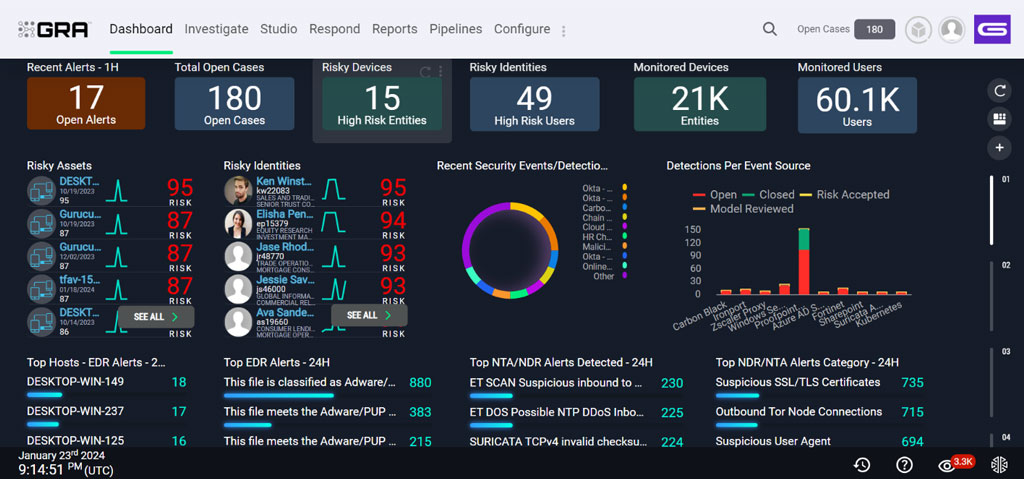
By Chaim Mazal, Chief Security Officer, Gigamon Over the last few years, organizations have been hearing about a Zero Trust architecture (ZTA) as a means for IT leaders to take a […]
The post Operationalizing Zero Trust Architecture appeared first on Cyber Defense Magazine.