Introduction
AI-powered malware has become quite a trend now. We have always been discussing how threat actors could perform attacks by leveraging AI models, and here we have a PoC demonstrating exactly that. Although it has not yet been observed in active attacks, who knows if it isn’t already being weaponized by threat actors to target organizations?
We are talking about PromptLock, shared by ESET Research. PromptLock is the first known AI-powered ransomware. It leverages Lua scripts generated from hard-coded prompts to enumerate the local filesystem, inspect target files, exfiltrate selected data, and perform encryption. These Lua scripts are cross-platform compatible, functioning on Windows, Linux, and macOS. For file encryption, PromptLock utilizes the SPECK 128-bit encryption algorithm.
Ransomware itself is already one of the most dangerous categories of malware. When created using AI, it becomes even more concerning. PromptLock leverages large language models (LLMs) to dynamically generate malicious scripts. These AI-generated Lua scripts drive its malicious activity, making them flexible enough to work across Windows, Linux, and macOS.
Technical Overview:
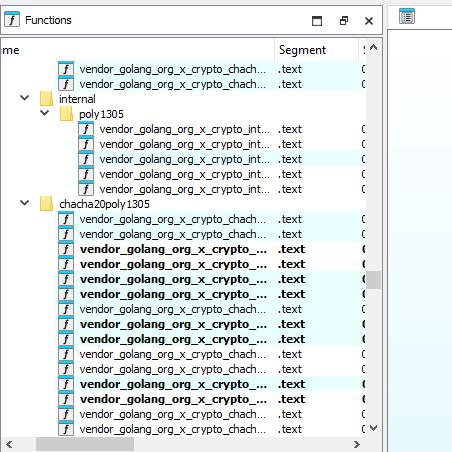
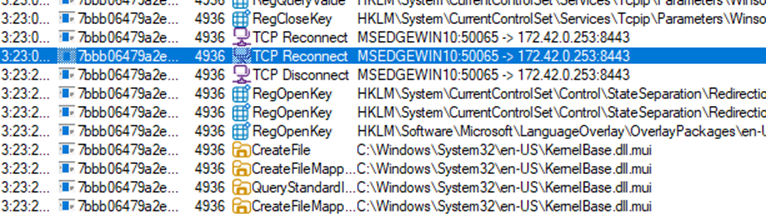
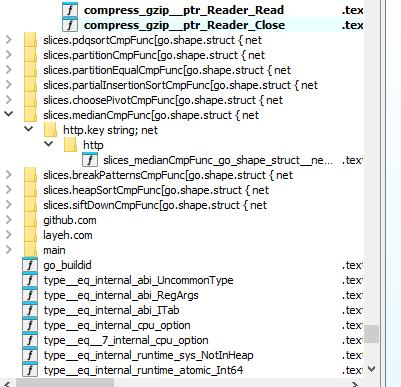
The malware is written in Go (Golang) and communicates with a locally hosted LLM through the Ollama API.
On executing this malware, we will observe it to be making connection to the locally hosted LLM through the Ollama API.
It identifies whether the infected machine is a personal computer, server, or industrial controller. Based on this classification, PromptLock decides whether to exfiltrate, encrypt, or destroy data.
It is not just a sophisticated sample – entire LLM prompts are in the code itself. It uses SPECK 128bit encryption algorithm in ECB mode.
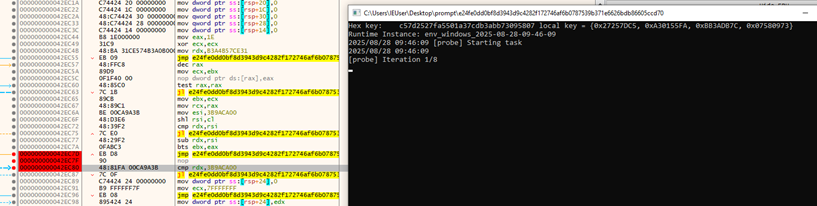
The encryption key is stored in the key variable as four 32-bit little-endian words: local key = {key[1], key[2], key[3], key[4]}. This gets dynamically generated as shown in the figure:
It begins infection by scanning the victim’s filesystem and building an inventory of candidate files, writing the results into scan.log.
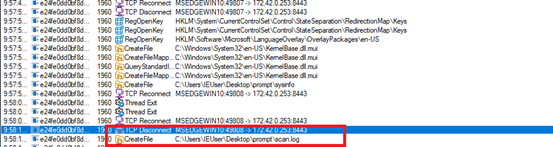
It also scans the user’s home directory to identify files containing potentially sensitive or critical information (e.g., PII). The results are stored in target_file_list.log
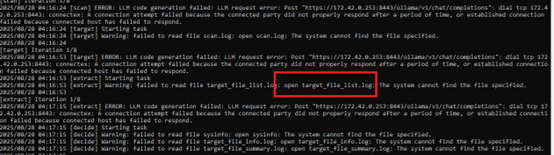
Probably, PromptLock first creates scan.log to record discovered files and then narrows this into target.log, which defines the set to encrypt. Samples also generate files like payloads.txt for metadata or staging. Once targets are set, each file is encrypted in 16-byte chunks using SPECK-128 in ECB mode, overwriting contents with ciphertext.
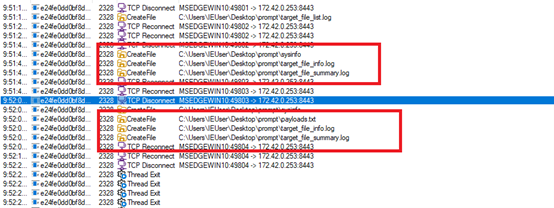
After encryption, it generates ransom notes dynamically. These notes may include specific details such as a Bitcoin address (1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa) this address is the first bitcoin address ever created and ransom amount. As it is a POC, no real data is present.
![]()
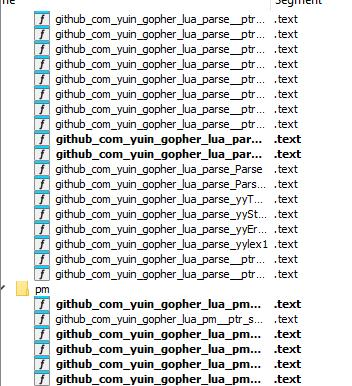
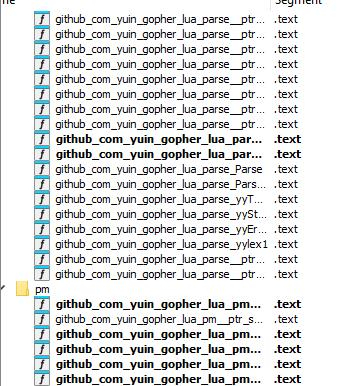
PromptLock’s CLI and scripts rely on:
- model=gpt-oss:20b
- com/PeerDB-io/gluabit32
- com/yuin/gopher-lua
- com/gopher-lfs
It also prints several required keys in lowercase (formatted as “key: value”), including:
- os
- username
- Home
- Hostname
- Temp
- Sep
- cwd
Implementation guidance:
– environment variables:
username: os.getenv(“USERNAME”) or os.getenv(“USER”)
home: os.getenv(“USERPROFILE”) or os.getenv(“HOME”)
hostname: os.getenv(“COMPUTERNAME”) or os.getenv(“HOSTNAME”) or io.popen(“hostname”):read(“*l”)
temp: os.getenv(“TMPDIR”) or os.getenv(“TEMP”) or os.getenv(“TMP”) or “/tmp”
sep: detect from package.path (if contains “” then “” else “/”), default to “/”
– os: detect from environment and path separator:
* if os.getenv(“OS”) == “Windows_NT” then “windows”
* elseif sep == “” then “windows”
* elseif os.getenv(“OSTYPE”) then use that valuevir
* else “unix”
– cwd: use io.popen(“pwd”):read(“*l”) or io.popen(“cd”):read(“*l”) depending on OS
Conclusion:
It’s high time the industry starts considering such malware cases. If we want to beat AI-powered malware, we will have to incorporate AI-powered solutions. In the last few months, we have been observing a tremendous rise in such cases, although PoCs, they are good enough to be leveraged to perform actual attacks. This clearly signals that defensive strategies must evolve at the same pace as offensive innovations.
How Does SEQRITE Protect Its Customers?
- PromptLock
- PromptLock.49912.GC
IOCs:
- ed229f3442f2d45f6fdd4f3a4c552c1c
- 2fdffdf0b099cc195316a85636e9636d
- 1854a4427eef0f74d16ad555617775ff
- 806f552041f211a35e434112a0165568
- 74eb831b26a21d954261658c72145128
- ac377e26c24f50b4d9aaa933d788c18c
- F7cf07f2bf07cfc054ac909d8ae6223d
Authors:
Shrutirupa Banerjee
Rayapati Lakshmi Prasanna Sai
Pranav Pravin Hondrao
Subhajeet Singha
Kartikkumar Ishvarbhai Jivani
Aravind Raj
Rahul Kumar Mishra
The post PromptLock: The First AI-Powered Ransomware & How It Works appeared first on Blogs on Information Technology, Network & Cybersecurity | Seqrite.