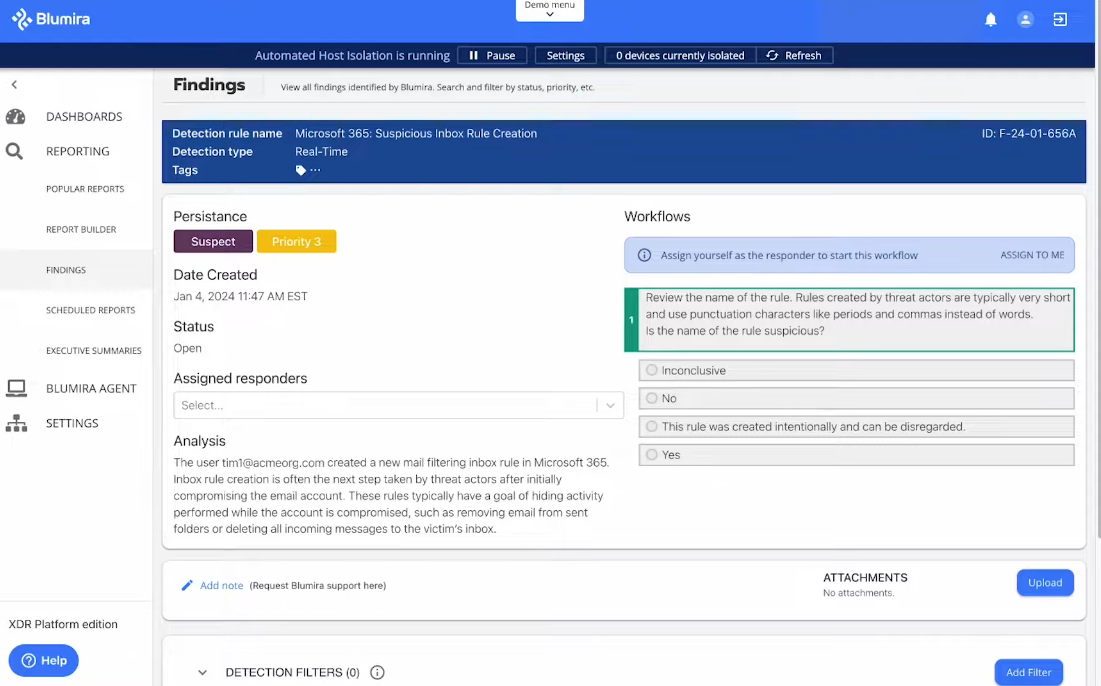
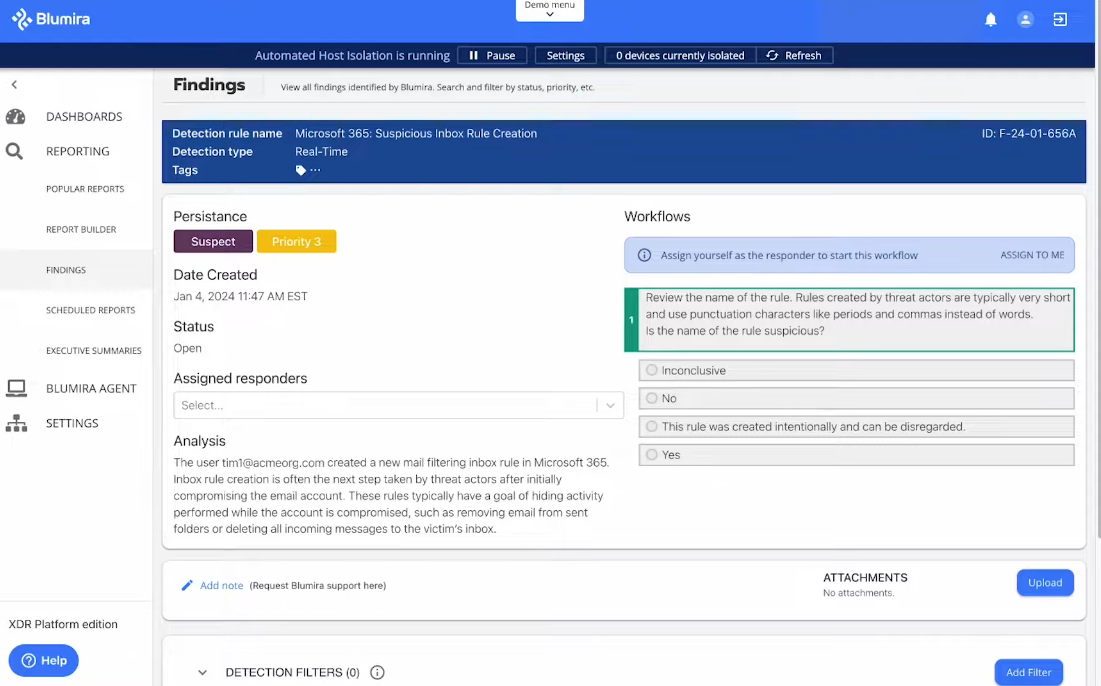
 I was thrilled to catch up with Blumira during Black Hat USA 2024. When it comes to resource-constrained businesses, traditional security information and event management (SIEM) systems can seem like…
I was thrilled to catch up with Blumira during Black Hat USA 2024. When it comes to resource-constrained businesses, traditional security information and event management (SIEM) systems can seem like…
The post Publishers Spotlight: Blumira appeared first on Cyber Defense Magazine.