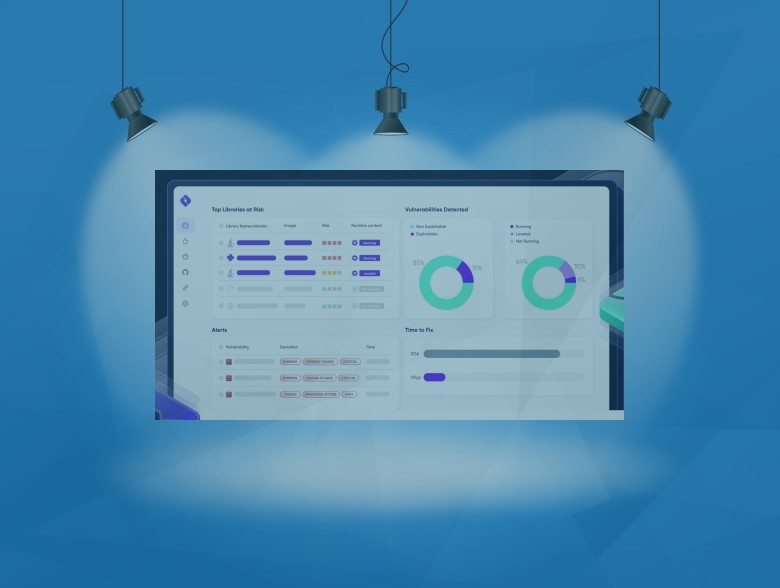
Oligo Security is one of the leading open source cybersecurity platforms, pioneering the next wave of application security with a runtime solution that is proactive, effective, and frictionless. Oligo found […]
The post Publisher’s Spotlight: Oligo: Protect Your Open Source Libraries appeared first on Cyber Defense Magazine.

