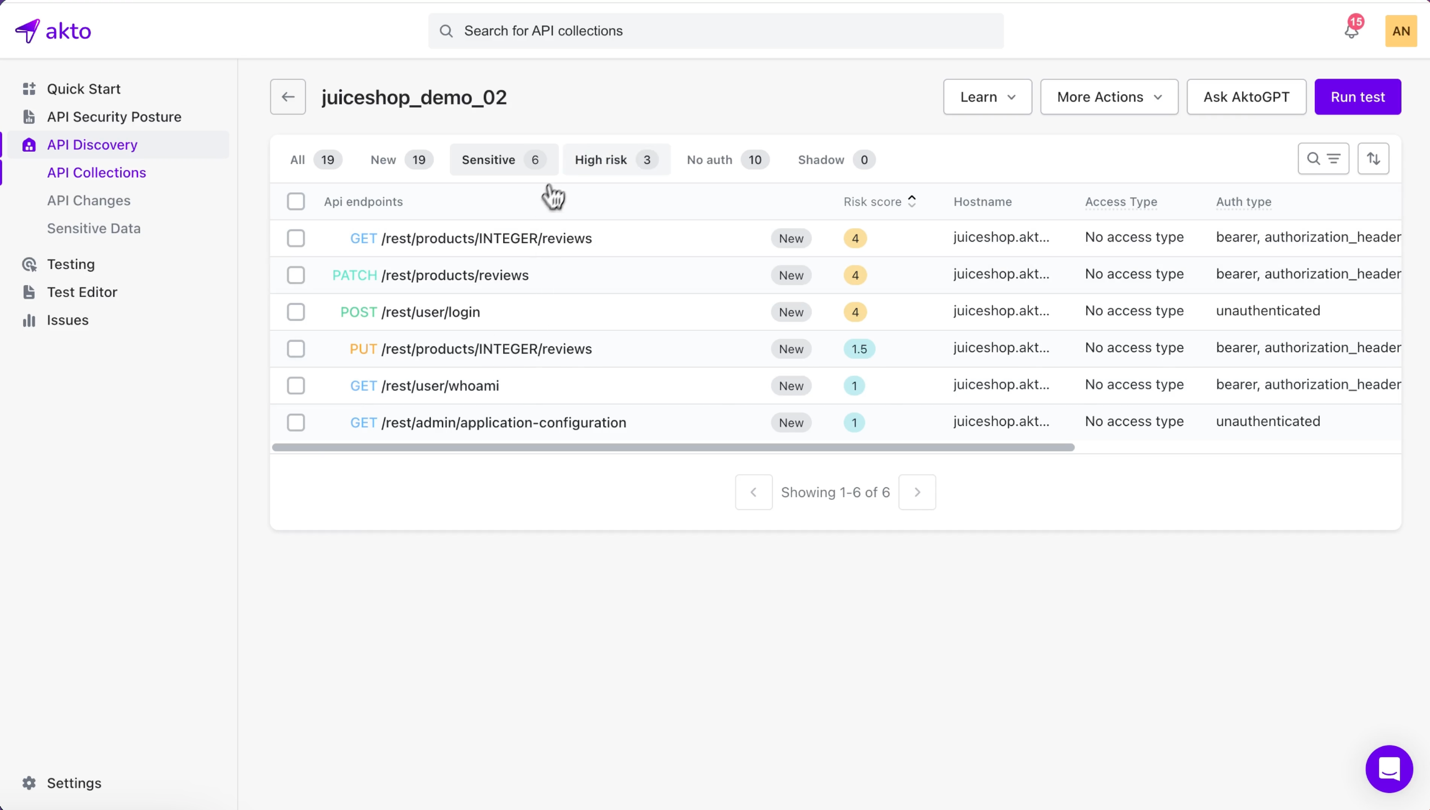
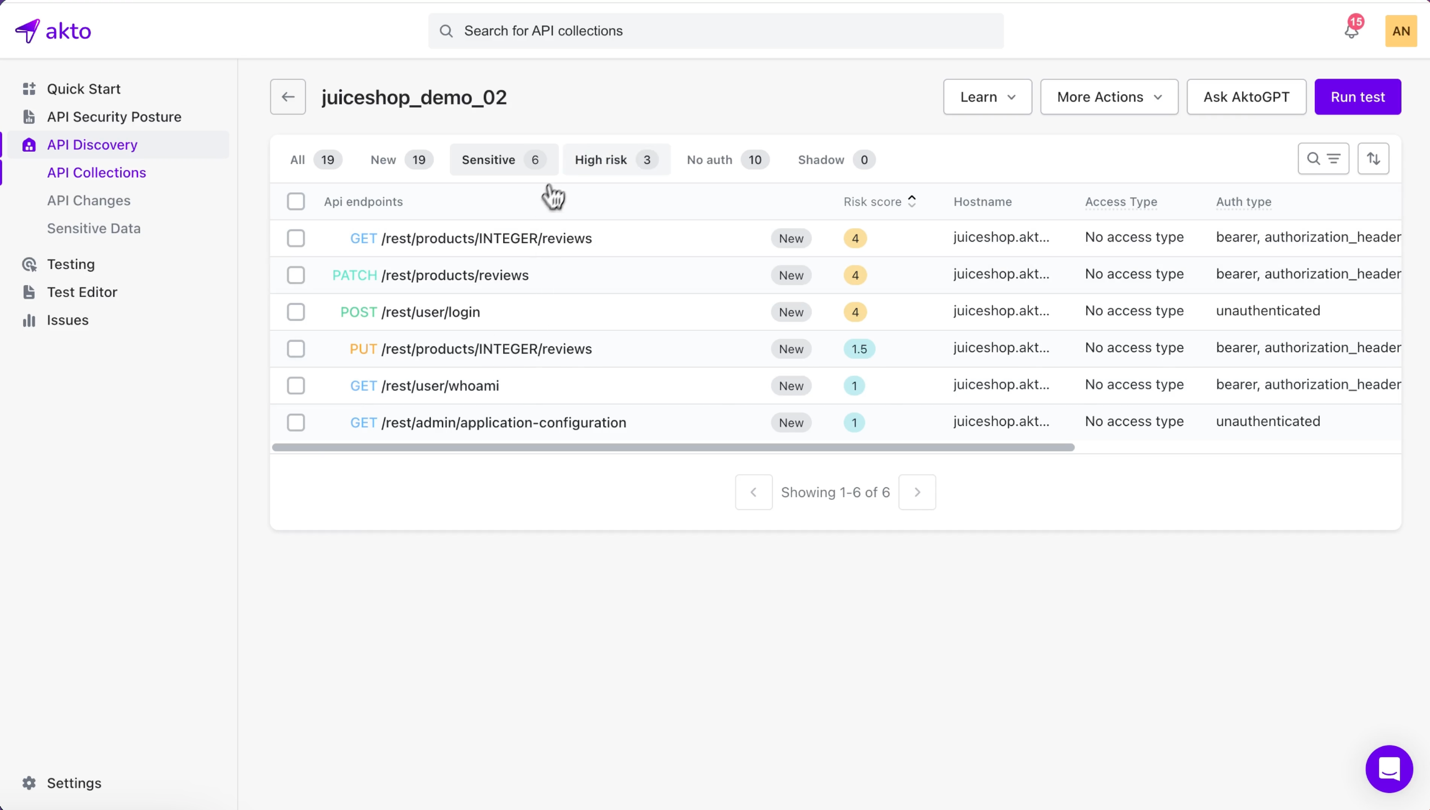
 As APIs become the backbone of digital transformation, they also represent one of the biggest security risks to organizations. According to Gartner, by 2025, APIs will be the top attack…
As APIs become the backbone of digital transformation, they also represent one of the biggest security risks to organizations. According to Gartner, by 2025, APIs will be the top attack…
The post Spotlight on Akto.ai appeared first on Cyber Defense Magazine.

