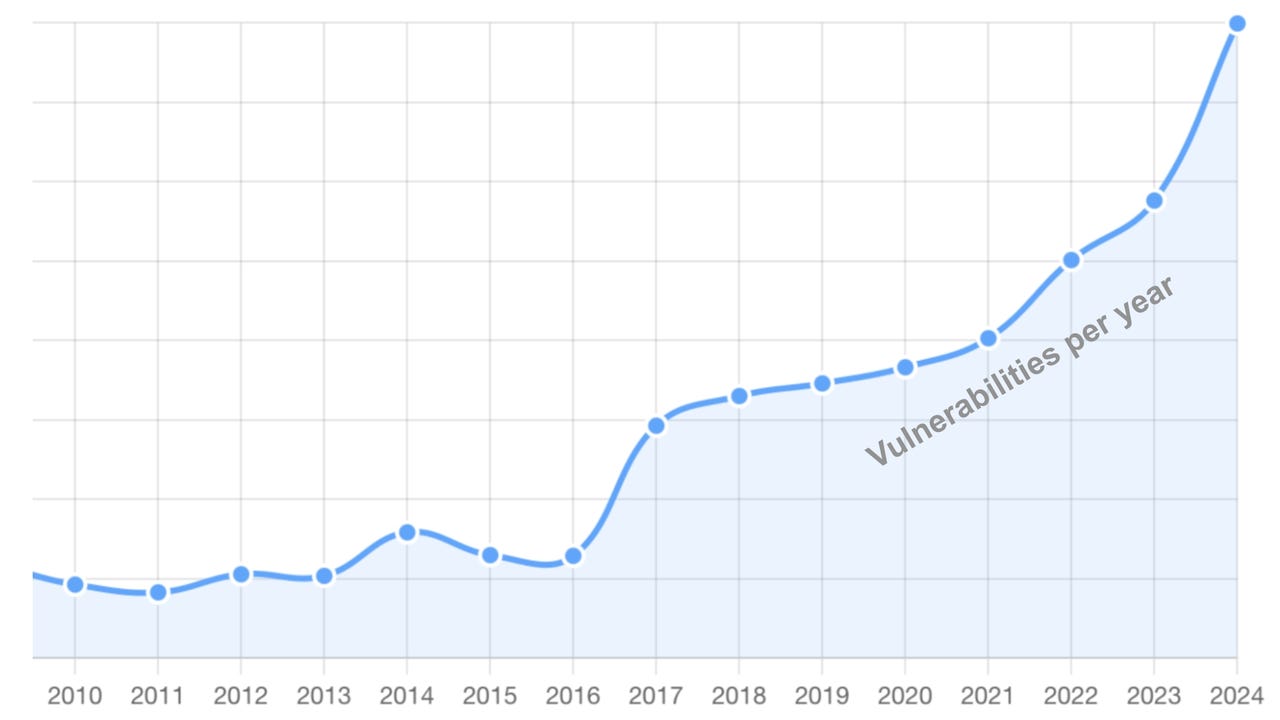
 By Jeff Hahn, principal of Hahn, and Kenneth Holley, Principal and chairman of Silent Quadrant With the increasing unpredictability and sophistication of cyber threats, IT and communications departments must align […]
By Jeff Hahn, principal of Hahn, and Kenneth Holley, Principal and chairman of Silent Quadrant With the increasing unpredictability and sophistication of cyber threats, IT and communications departments must align […]
The post The Cybersecurity Bridge: A Necessary Connection for IT and Communications appeared first on Cyber Defense Magazine.