By Caroline McCaffery, Co-Founder and CEO of ClearOPS Introduction to Vendor Management Why does every license agreement and data protection addendum, suddenly, include a right for the buyer to perform […]
By Caroline McCaffery, Co-Founder and CEO of ClearOPS Introduction to Vendor Management Why does every license agreement and data protection addendum, suddenly, include a right for the buyer to perform […]
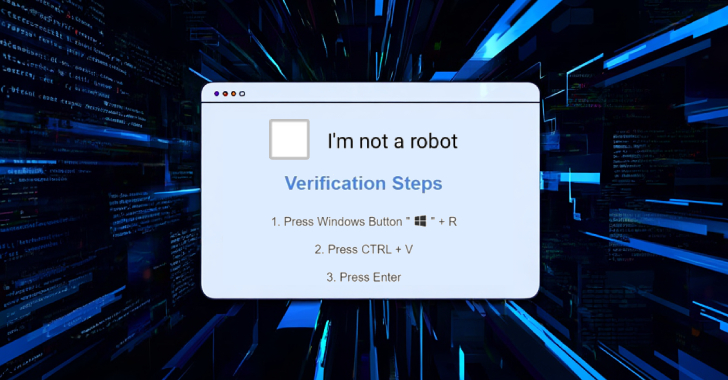
The post Vendors Beware of the Cybersecurity Audit appeared first on Cyber Defense Magazine.