The post What Is PAM-as-a-Service (PAMaaS)? appeared first on Heimdal Security Blog.
Related Posts
If you’re looking for PDQ Deploy alternatives, you’re either aware…
- rooter
- March 14, 2025
- 1 min read
- 0
By Jaye Tillson, Director of Strategy, Axis Security Evolution of…
- rooter
- June 14, 2023
- 1 min read
- 0
Digital signatures add your verified digital identity to outgoing emails…
- rooter
- March 28, 2023
- 1 min read
- 0
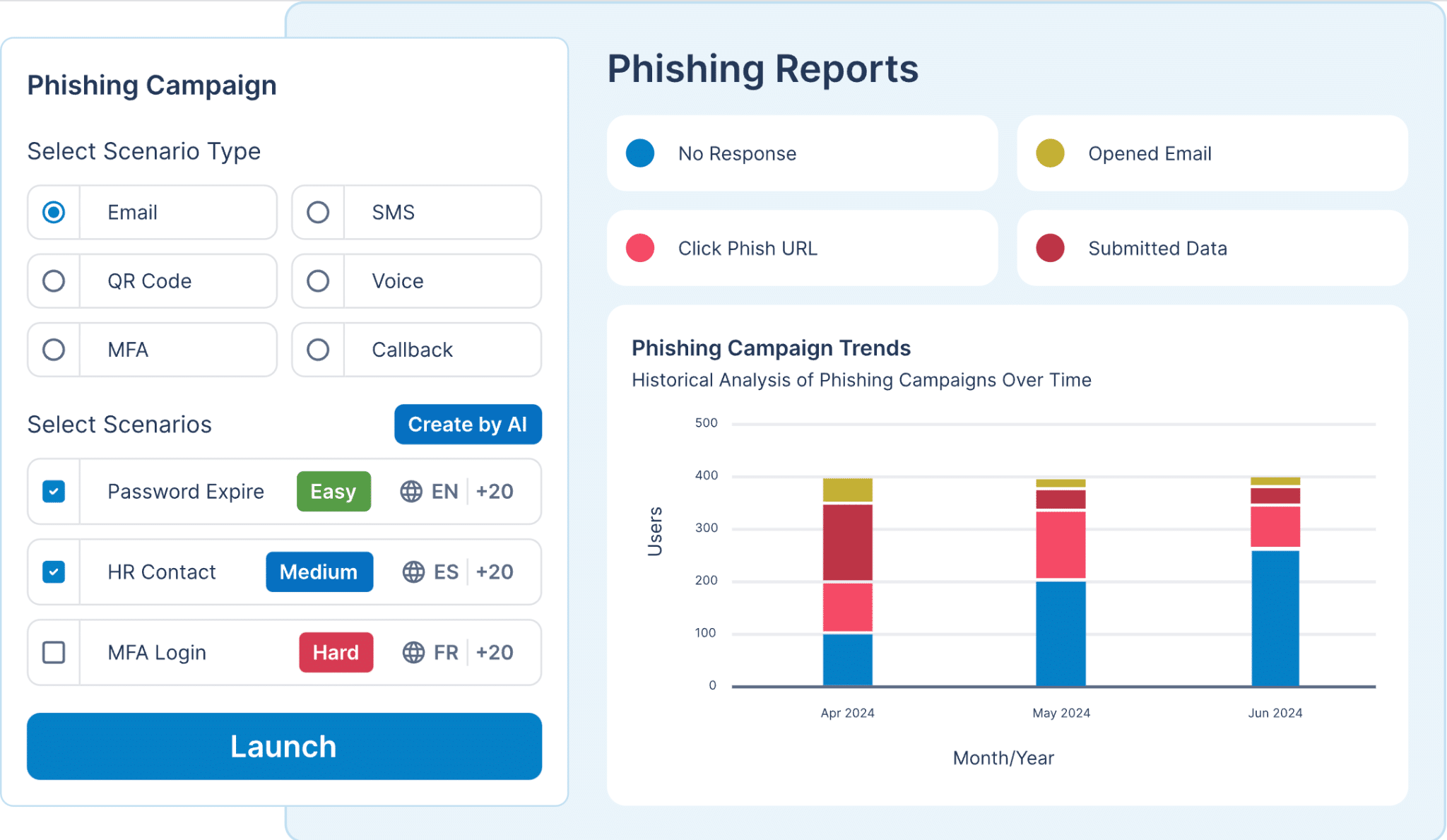
Human error remains one of the most significant vulnerabilities in…
- rooter
- September 11, 2024
- 1 min read
- 0