The post What is Phishing? Attack Techniques & Prevention Tips appeared first on GRC Solutions.
Related Posts
Western Digital announced that they discovered a network breach had…
- rooter
- April 4, 2023
- 1 min read
- 0
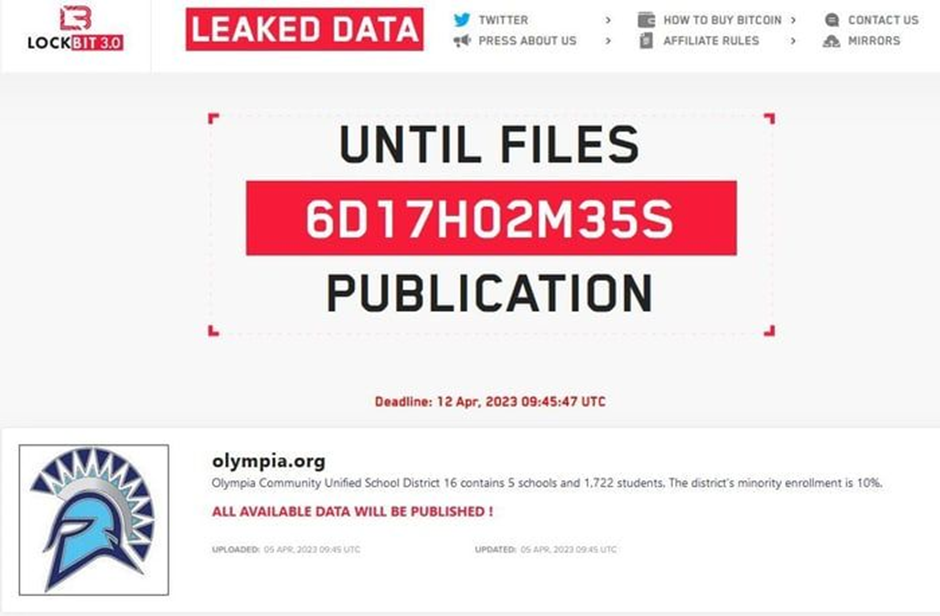
Last month, a school district in Illinois was targeted in…
- rooter
- May 4, 2023
- 4 min read
- 0
Model monitoring is essential for assuring the effectiveness and dependability…
- rooter
- May 16, 2023
- 1 min read
- 0
Hey there, fellow digital explorers! Welcome to a journey that…
- rooter
- August 24, 2023
- 1 min read
- 0