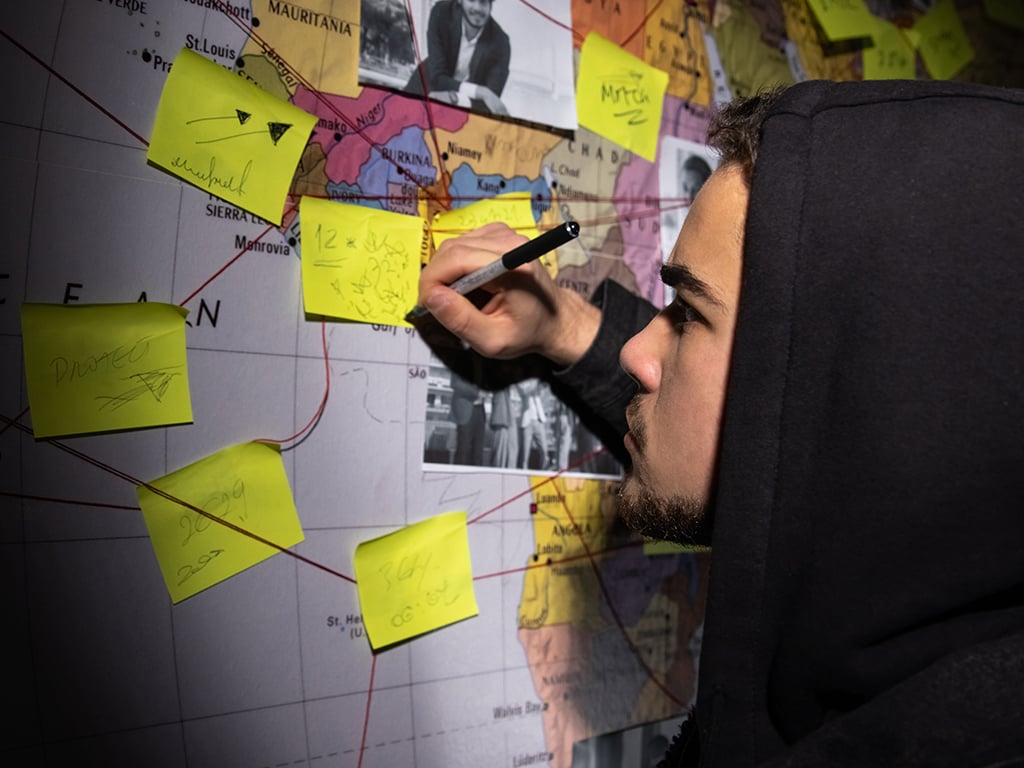
If your organization doesn’t already make security a pillar of its culture, this could be the year to start. That’s because the cybersecurity landscape is changing, due to factors including…
If your organization doesn’t already make security a pillar of its culture, this could be the year to start. That’s because the cybersecurity landscape is changing, due to factors including…
The post Your Company Culture Can Become A Powerful Cybersecurity Resource appeared first on Cyber Defense Magazine.