The post NIS2 Compliance Checklist appeared first on Heimdal Security Blog.
Related Posts
Agentic AI adoption and identity security risks, IGA expands in…
- rooter
- December 31, 2025
- 1 min read
- 0
Welcome to our January 2023 list of data breaches and…
- rooter
- February 20, 2023
- 6 min read
- 0
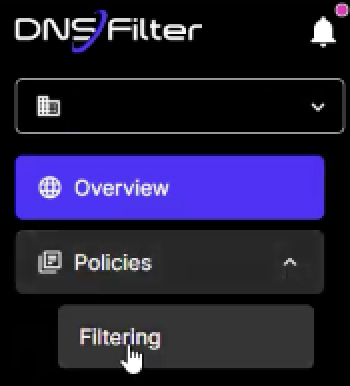
This HowTo article shows how to allow-list in DNS Filter.…
- rooter
- September 11, 2025
- 1 min read
- 0
“Shift-left” is a familiar concept to CISOs and security practitioners…
- rooter
- January 8, 2025
- 1 min read
- 0